700 Cutting-Edge Hacker Names to Define Your Cyber Identity
Por um escritor misterioso
Descrição
we have compiled a list of 700 creative hacker names that are sure to pique your interest. So Let's dive into

Machine learning and blockchain technologies for cybersecurity in connected vehicles - Ahmad - WIREs Data Mining and Knowledge Discovery - Wiley Online Library

Data Security Data Science Dojo

Hackers: How many types are there? – Network Kings

6 Biggest Cybersecurity Breaches of Last Decade Shocking Cybersecurity Stats - Phoenix Security

DeFi hacks are worse than ever, Chainalysis and PeckShield report - Protocol
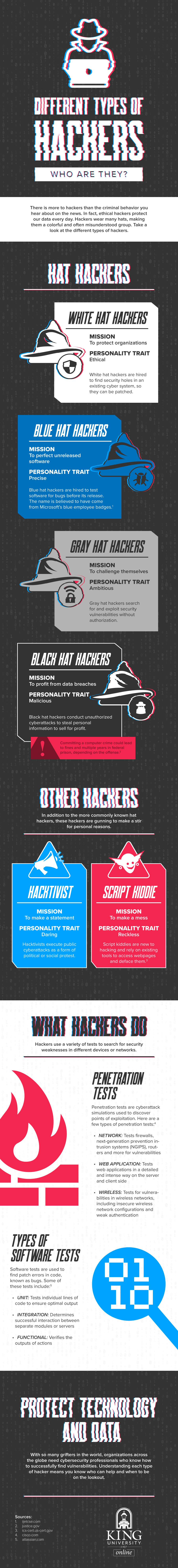
Different Types of Hackers: Who Are They?

Aether Global Innovations: Revolutionizing Drone Management, Monitoring and Surveillance Services for Industrial and Critical Infrastructure Operators

Better Security with Asset Inventory and Attack Surface Visibility - Spiceworks

Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It eBook : Goodman, Marc: Kindle Store

Top Mobile Security Threats (2023) — Mobile Device Security
de
por adulto (o preço varia de acordo com o tamanho do grupo)




/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2022/A/d/yxnZLsSEKneFvRlJJwgA/image-7-.png)
