Efficient detection of hacker community based on twitter data
Por um escritor misterioso
Descrição
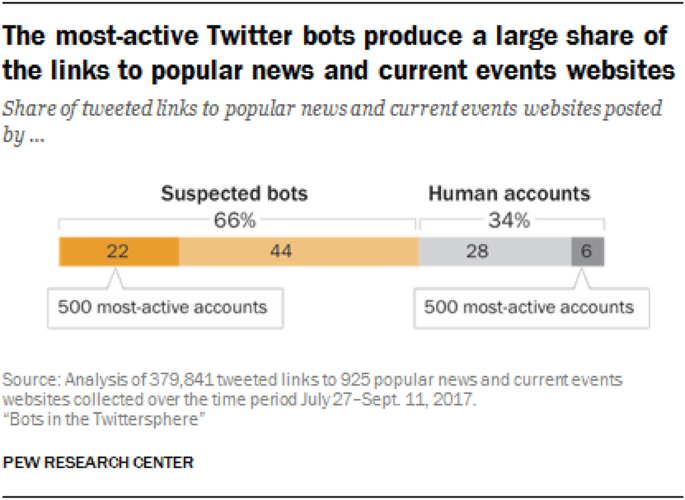
Twitter is one of the most popular platforms used to share and post ideas. Hackers and anonymous attackers use these platforms maliciously, and their behavior can be used to predict the risk of future attacks, by gathering and classifying hackers’ tw
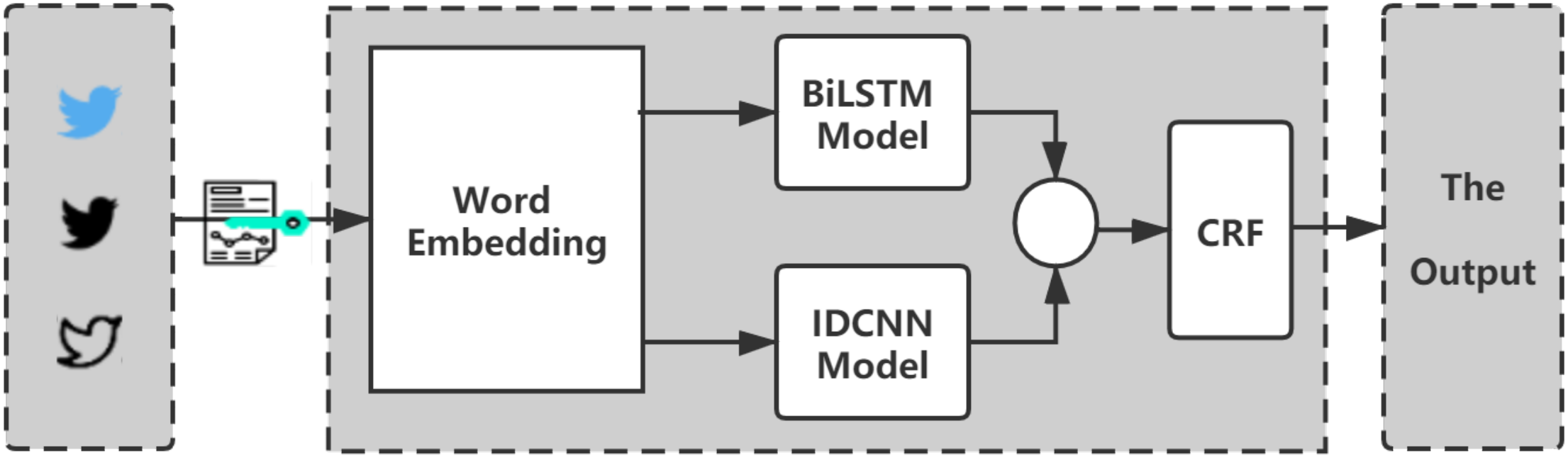
DeeProBot: a hybrid deep neural network model for social bot detection based on user profile data

Silent Surveillance Attack: How Hackers Can Use Wi-Fi to Track You Inside Your Home
Applied Sciences, Free Full-Text
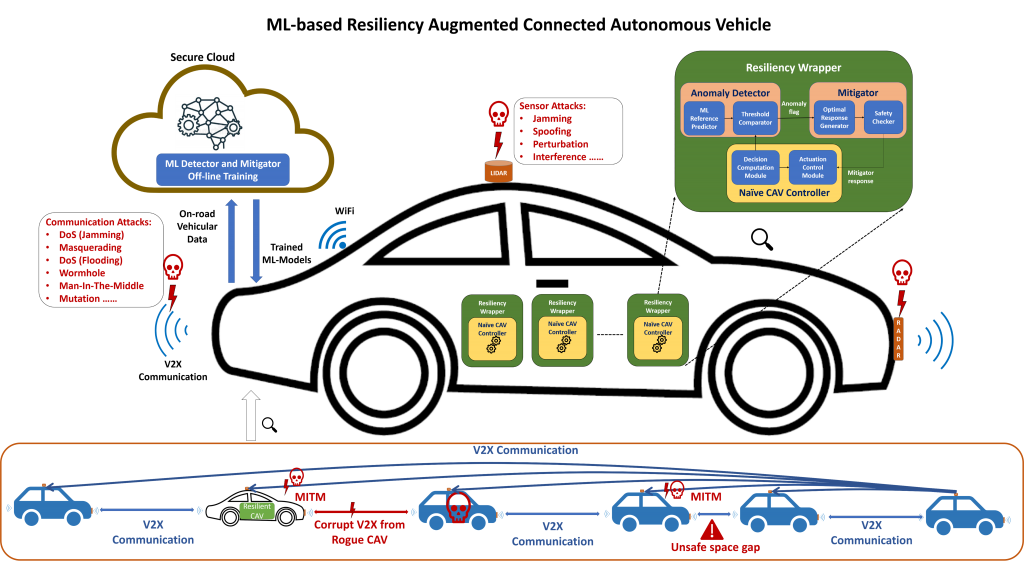
CAV

AI And Cybersecurity: Are We Fueling Hackers' Fire?
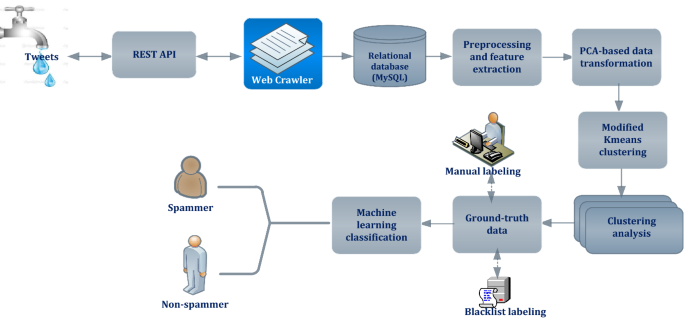
Twitter spam account detection based on clustering and classification methods
AI in Cyber Security: Advantages, Applications andUse Cases

The holy grail of note-taking: Private data, efficient methodology and P2P encrypted sync across all your devices - DEV Community

PDF) Efficient detection of hacker community based on twitter data using complex networks and machine learning algorithm
/f/137721/640x360/becd3b85e8/twitterhack.jpg)
A Lesson From Twitter's Data Breach Nightmare

6 Steps to Successful And Efficient Threat Hunting
de
por adulto (o preço varia de acordo com o tamanho do grupo)