Indirect Command Execution – Penetration Testing Lab
Por um escritor misterioso
Descrição
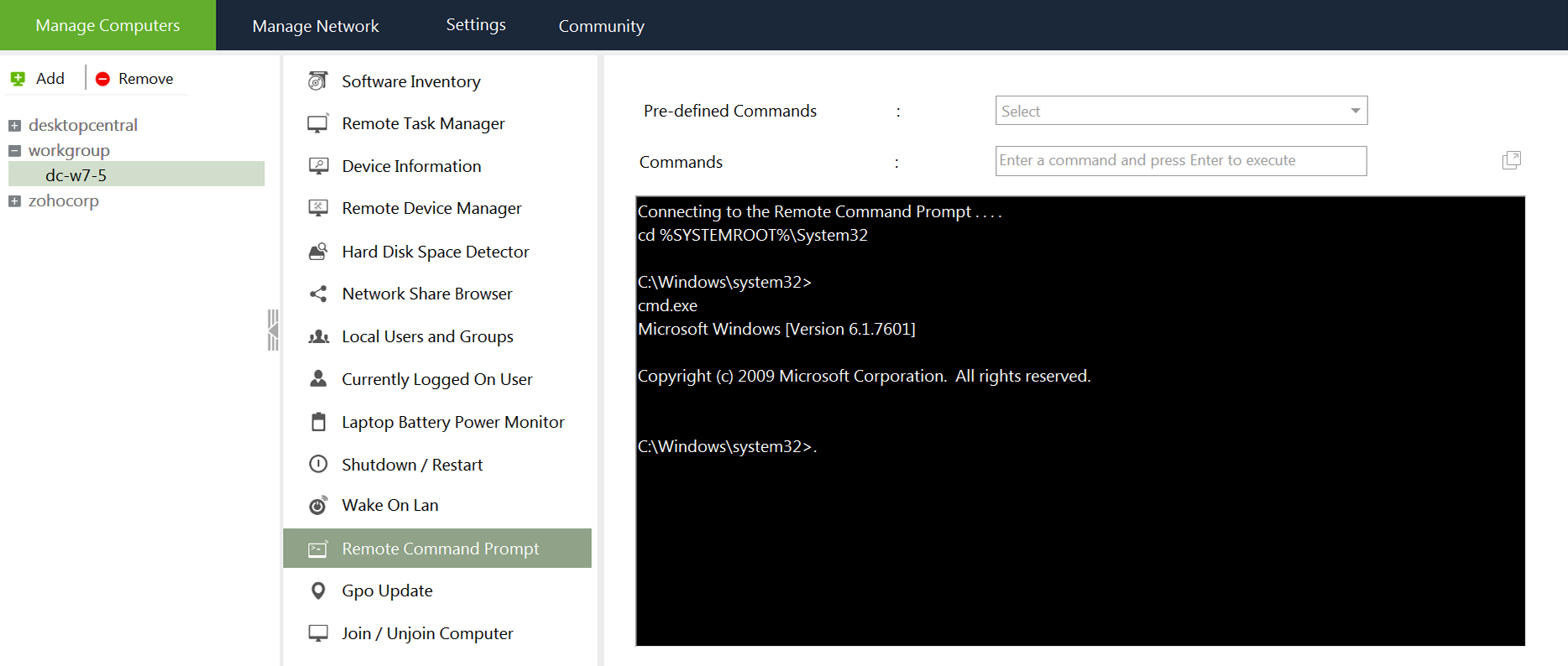
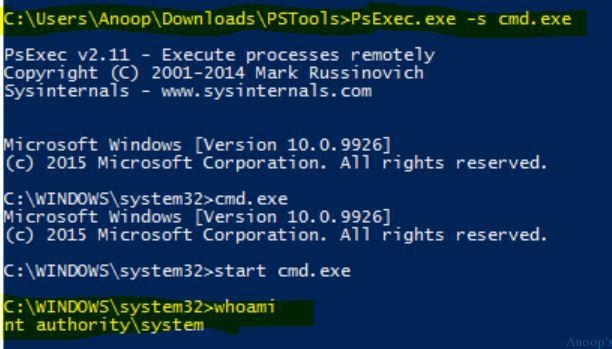
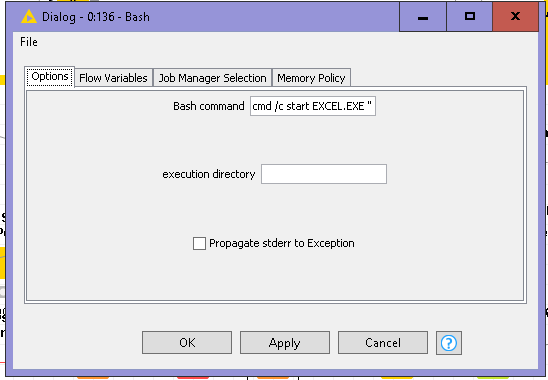
The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as "cmd.exe". In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or…

How to Prevent SQL Injection Attacks?

File Inclusion Vulnerabilities: What are they and how do they work?

OWASP LLM02: Insecure Output Handling
Information disclosure vulnerabilities

T1202: Indirect Command Execution - Red Team Notes 2.0

Spyse – A Cyber Security Search Engine – Penetration Testing Lab
Penetration Testing Lab 15 by Pentestit — walkthrough

Writing Exploits for Win32 Systems from Scratch, NCC Group Research Blog

Denial-of-service attack - Wikipedia
Securing LLM Systems Against Prompt Injection

TryHackMe Hacktivities

Indirect Command Execution – Penetration Testing Lab
de
por adulto (o preço varia de acordo com o tamanho do grupo)