How Do MAC Spoofing Attacks Work?
Por um escritor misterioso
Descrição
In this blog, we will go into the complexities of MAC spoofing, analyzing its repercussions and emphasizing the importance of having strong security policies in place.
What is Address Resolution Protocol? ARP Solutions - ManageEngine OpUtils
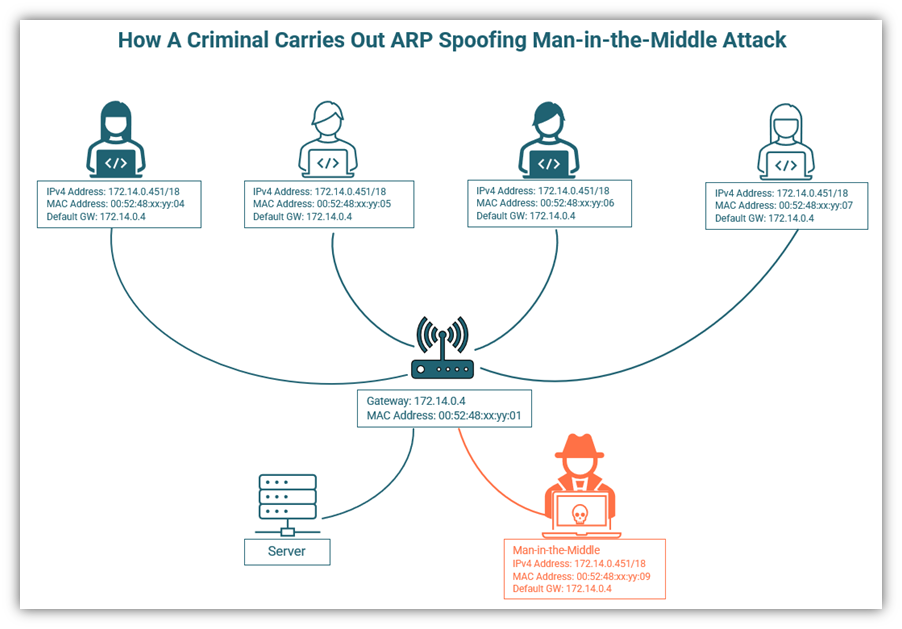
8 Types of Man in the Middle Attacks You Need to Know About

Lesson 9 - Securing the Local Area Network
What Is a MAC Spoofing Attack and How Can You Prevent It?
How Do MAC Spoofing Attacks Work?
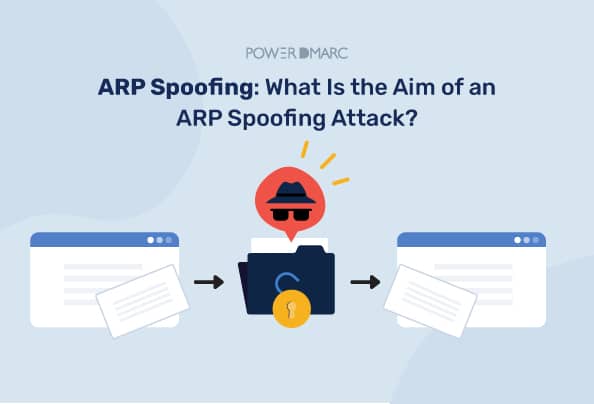
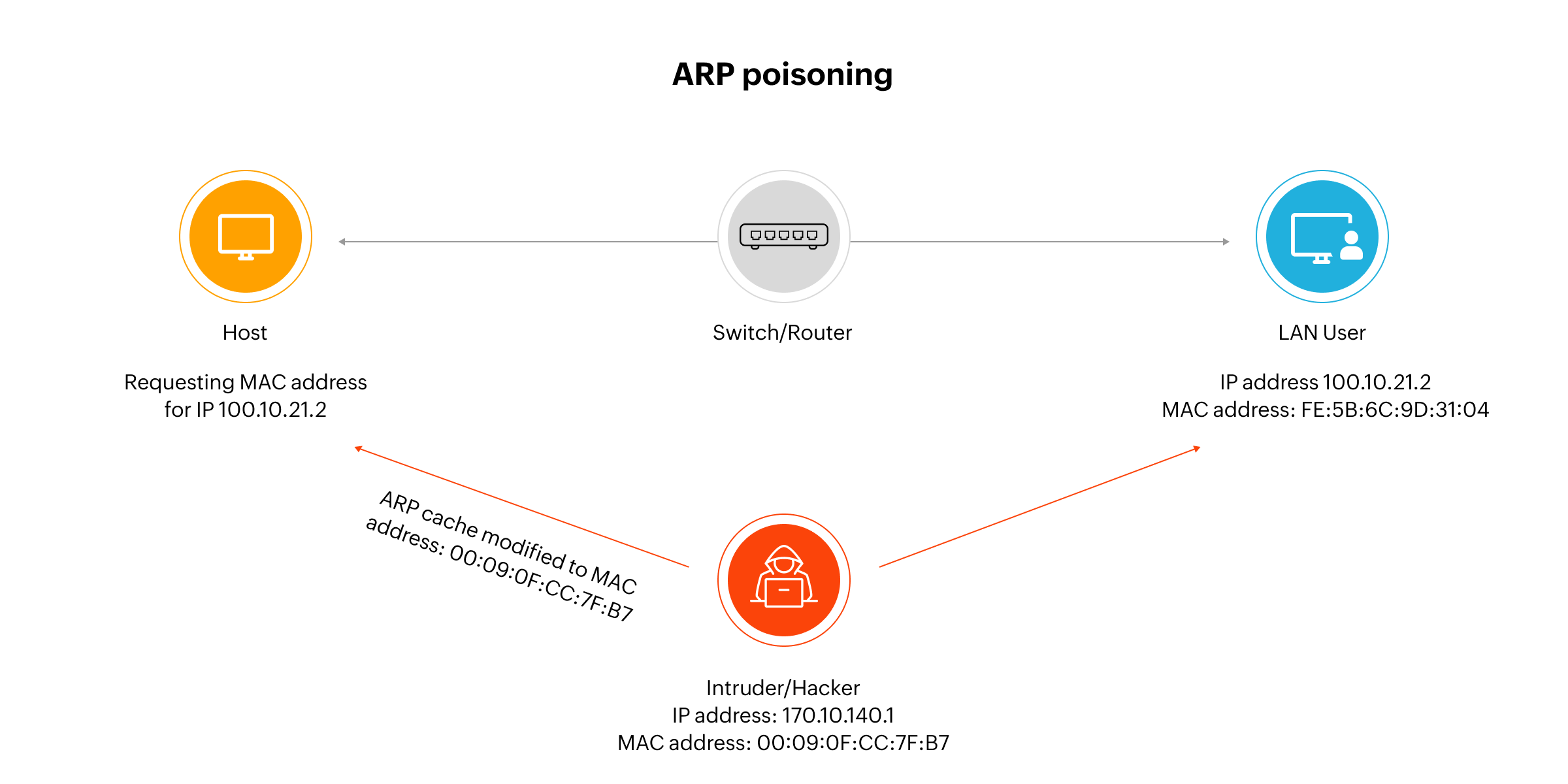
ARP Spoofing: What Is the Aim of an ARP Spoofing Attack?
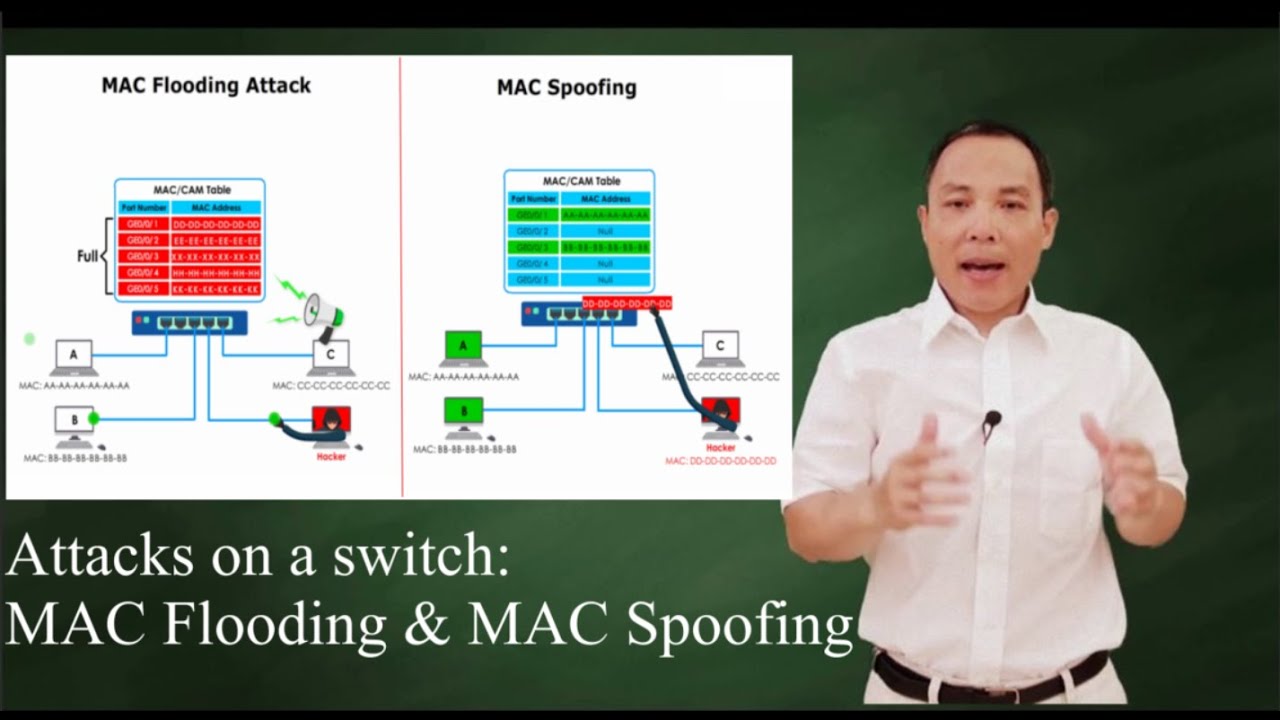
Switch attacks: MAC Flooding and MAC Spoofing
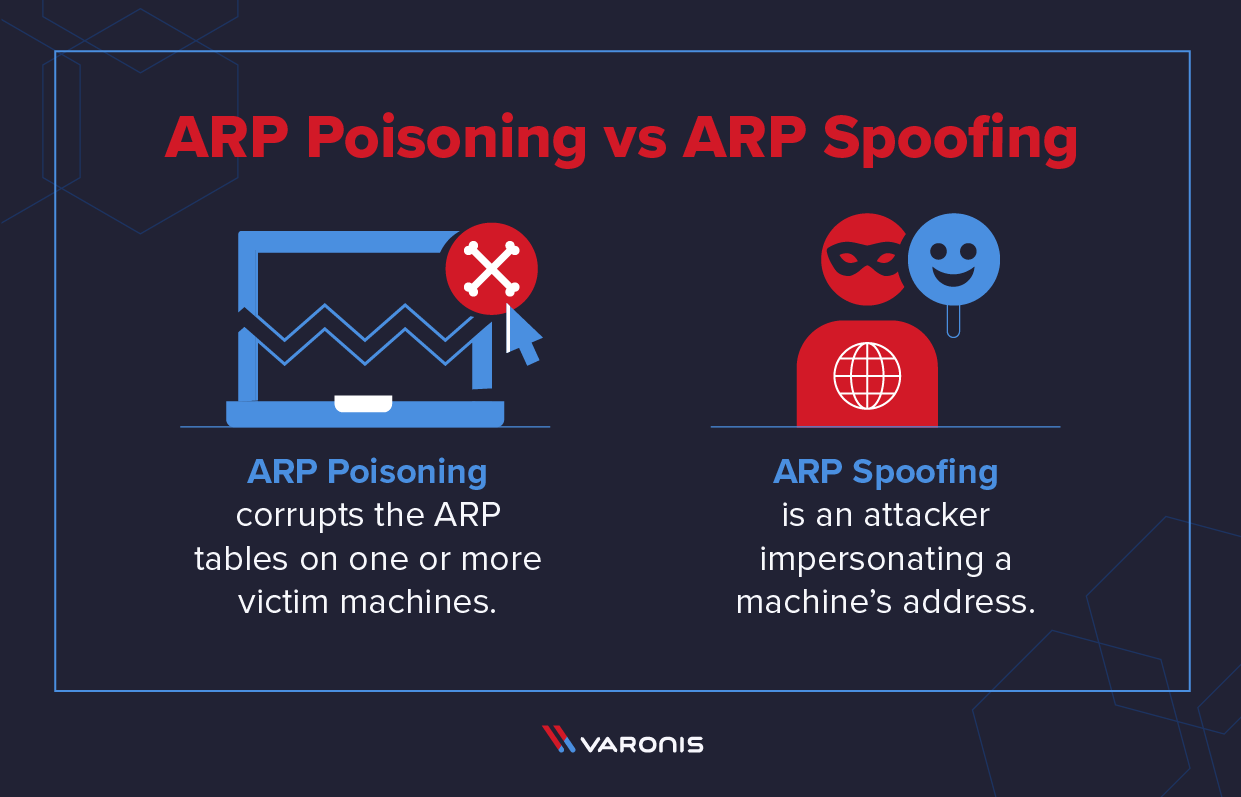
ARP Poisoning: What it is & How to Prevent ARP Spoofing Attacks
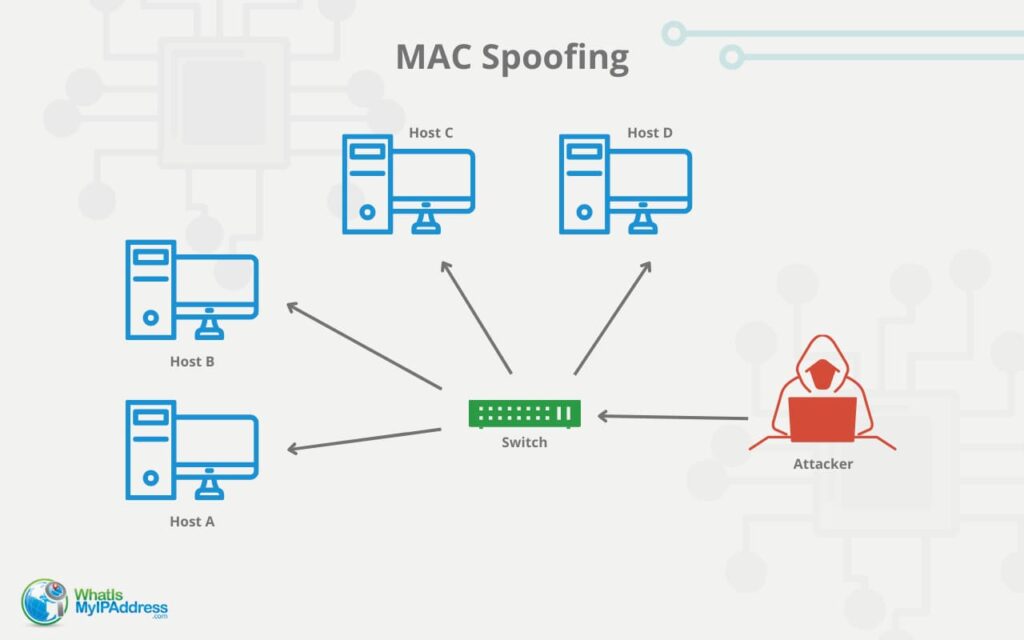
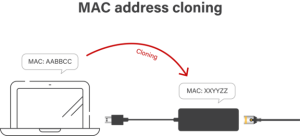
What is MAC Address Spoofing and How it Works
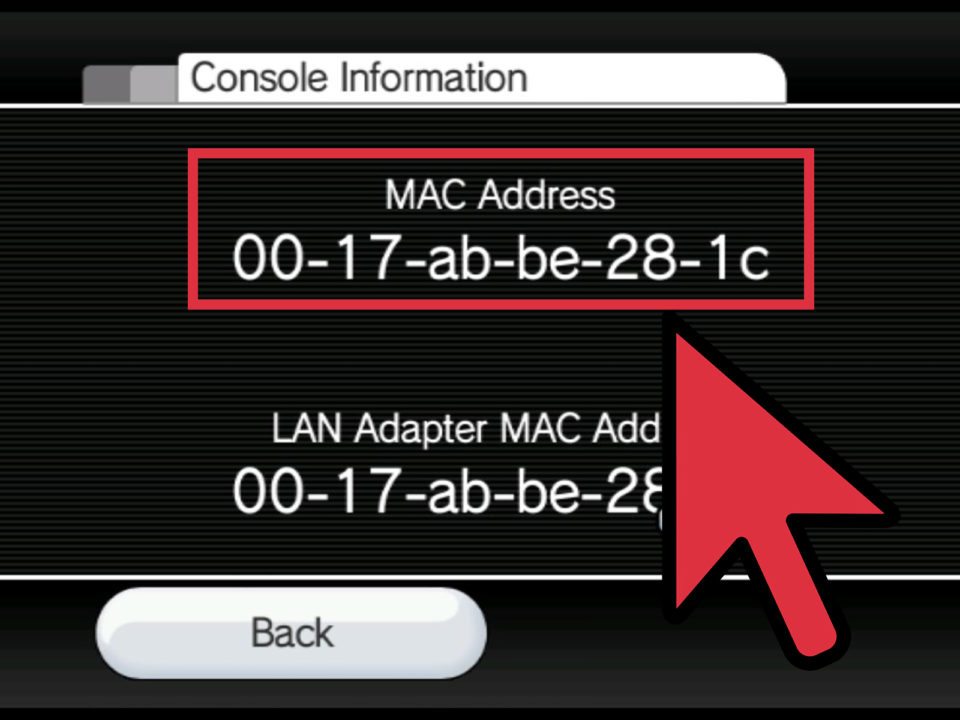
MAC ATTACK: How to Spoof your MAC Address - Electronics For You
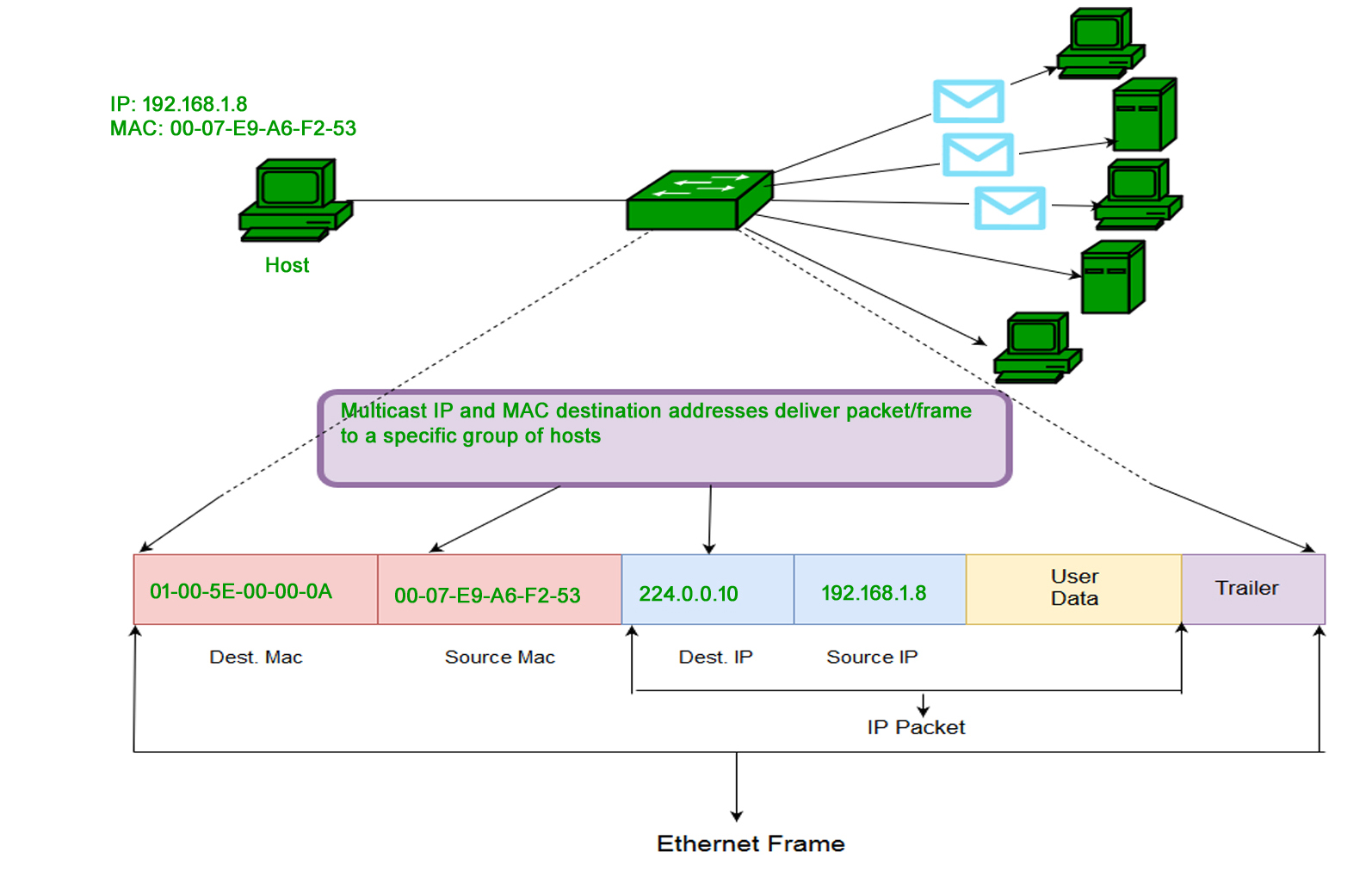
What is MAC Address? - GeeksforGeeks
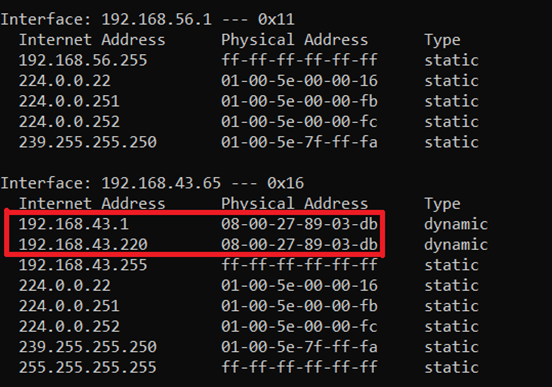
Everything You Need to Know About ARP Spoofing - Hashed Out by The SSL Store™
de
por adulto (o preço varia de acordo com o tamanho do grupo)