Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware analysis lockysample.bin.zip Malicious activity

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog
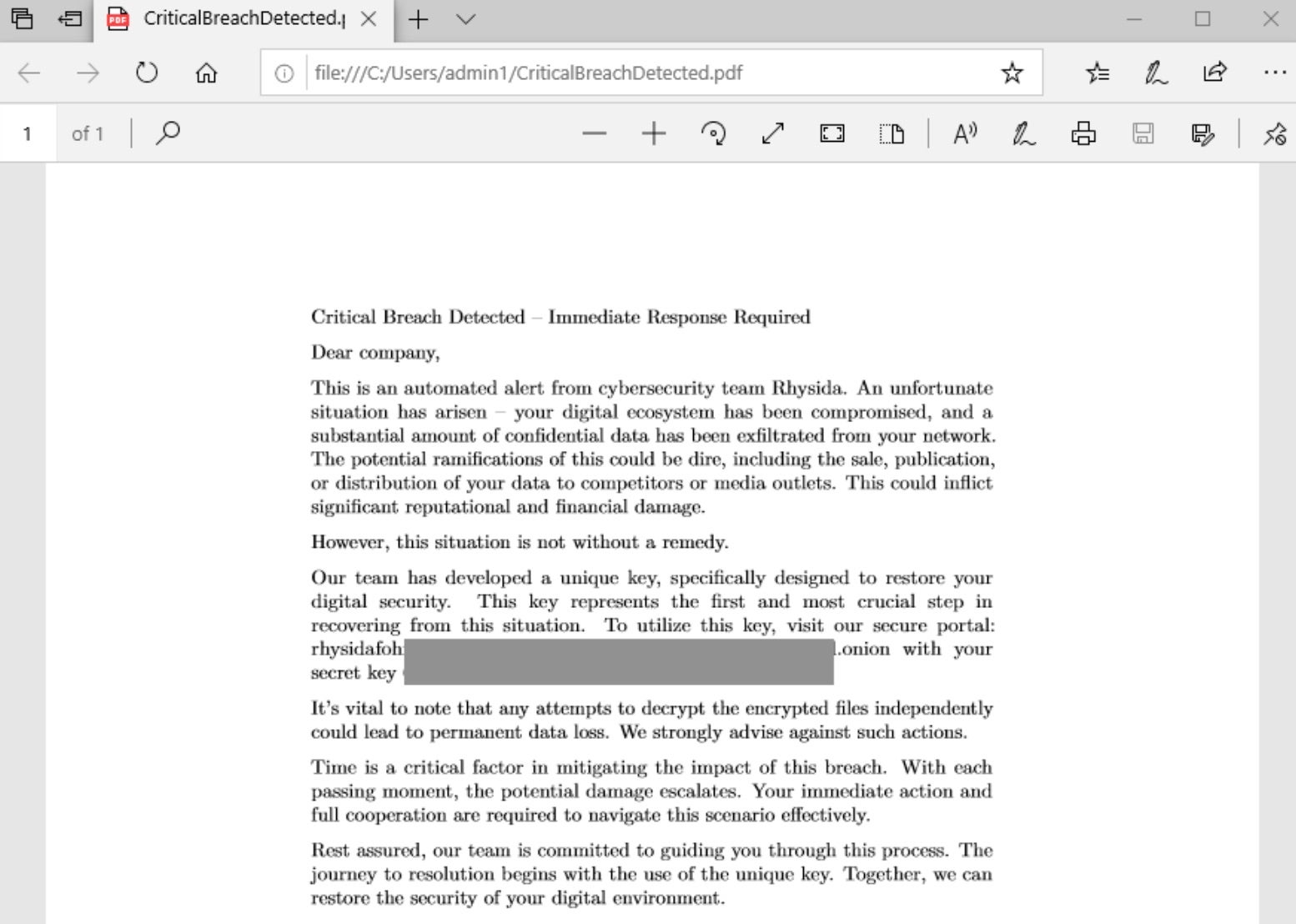
Rhysida - SentinelOne

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

How to Analyze Malware's Network Traffic in A Sandbox
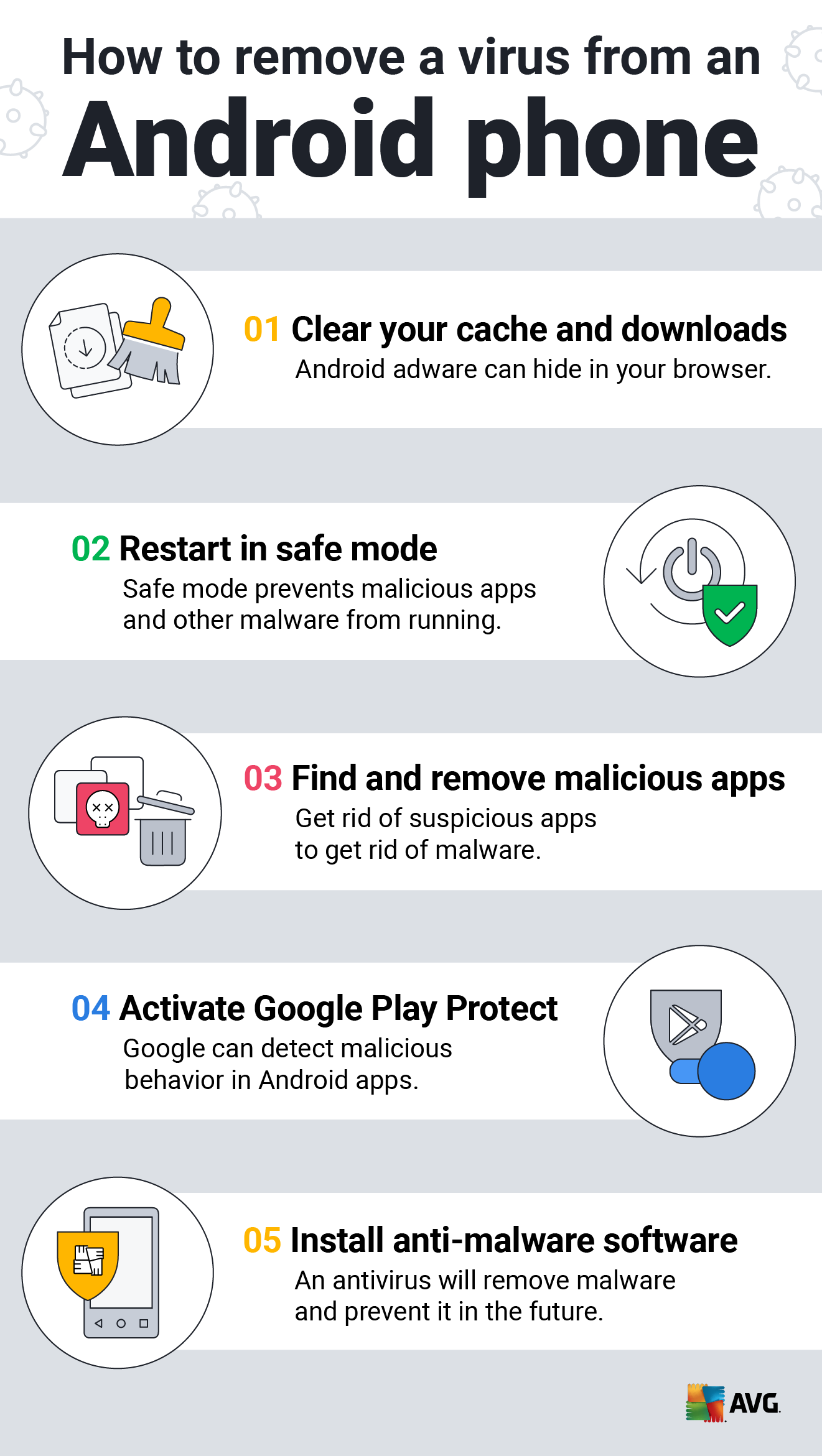
How to Clean an Android or iPhone from Viruses for Free

Malware analysis Program_Install_and_Uninstall Malicious activity

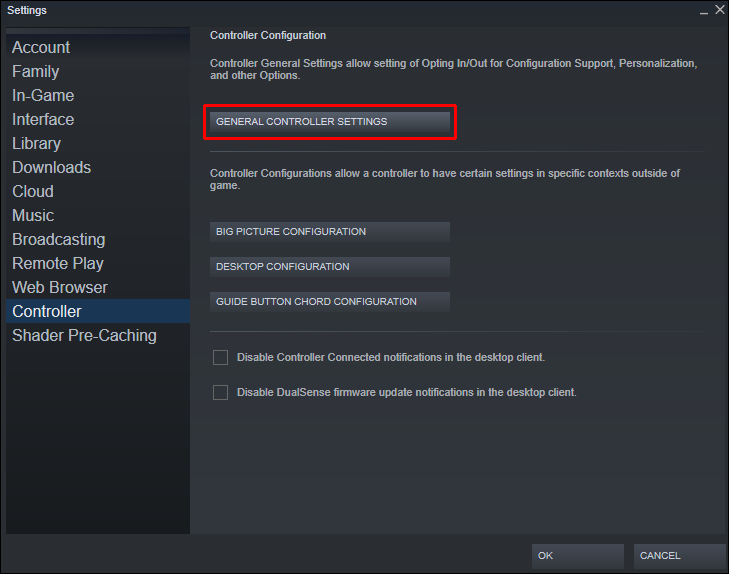
Endpoint Detection and Response, Free - What is EDR Security?

How to build a malware analysis sandbox with Elastic Security

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Cybersecurity Search Engine

Malware Analysis Benefits Incident Response
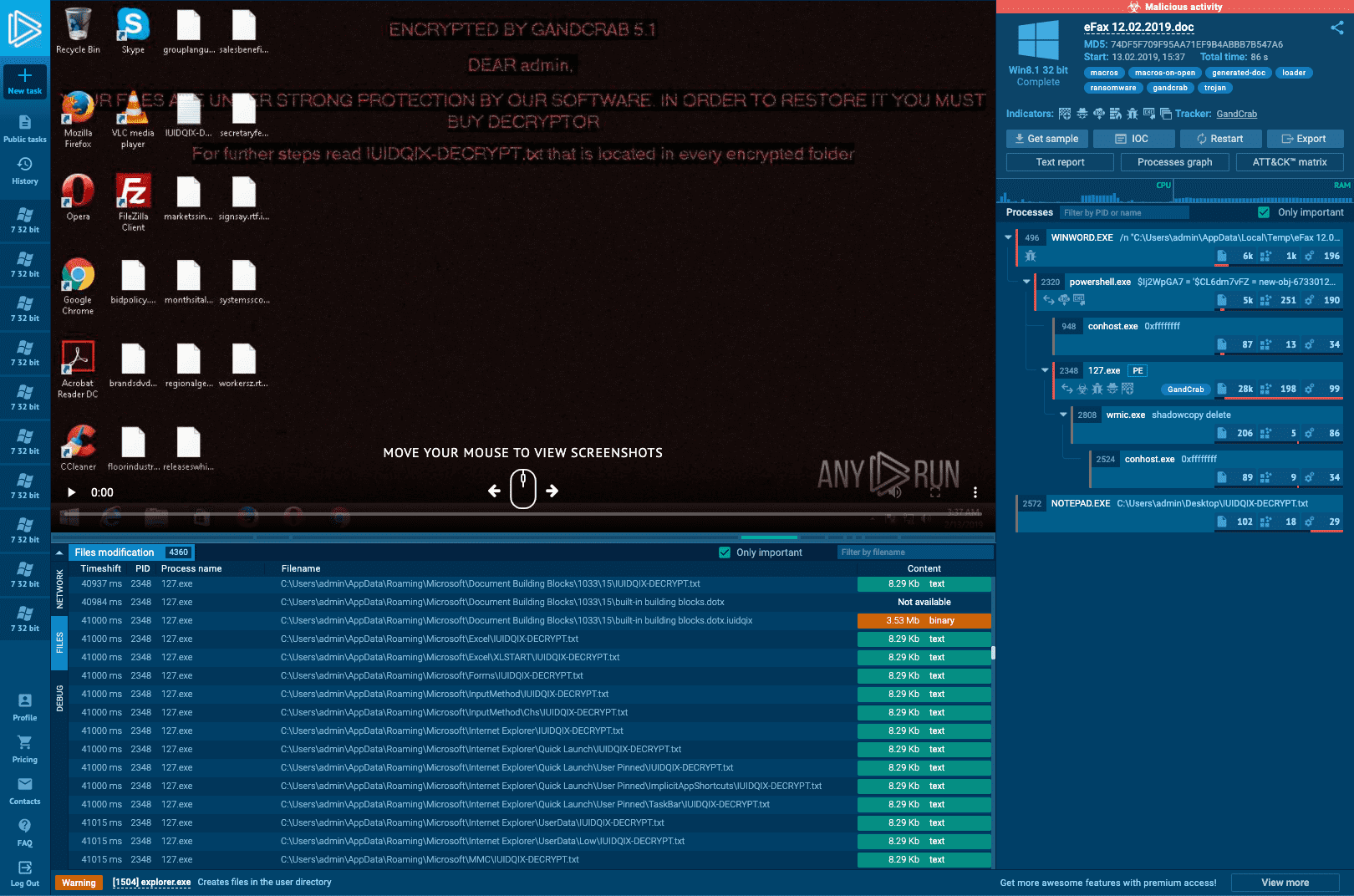
Interactive Online Malware Sandbox

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks
de
por adulto (o preço varia de acordo com o tamanho do grupo)