Malware analysis Malicious activity
Por um escritor misterioso
Descrição

What Is Malware Analysis? Definition, Types, Stages, and Best

How to Do Malware Analysis?

Endpoint Detection and Response, Free - What is EDR Security?
Malware analysis Malicious

Endpoint Detection and Response, Free - What is EDR Security?

PROUD-MAL: static analysis-based progressive framework for deep

Malware analysis

Info stealers and how to protect against them

Cybersecurity Search Engine

Interactive Online Malware Sandbox

Malware Analysis: Steps & Examples - CrowdStrike
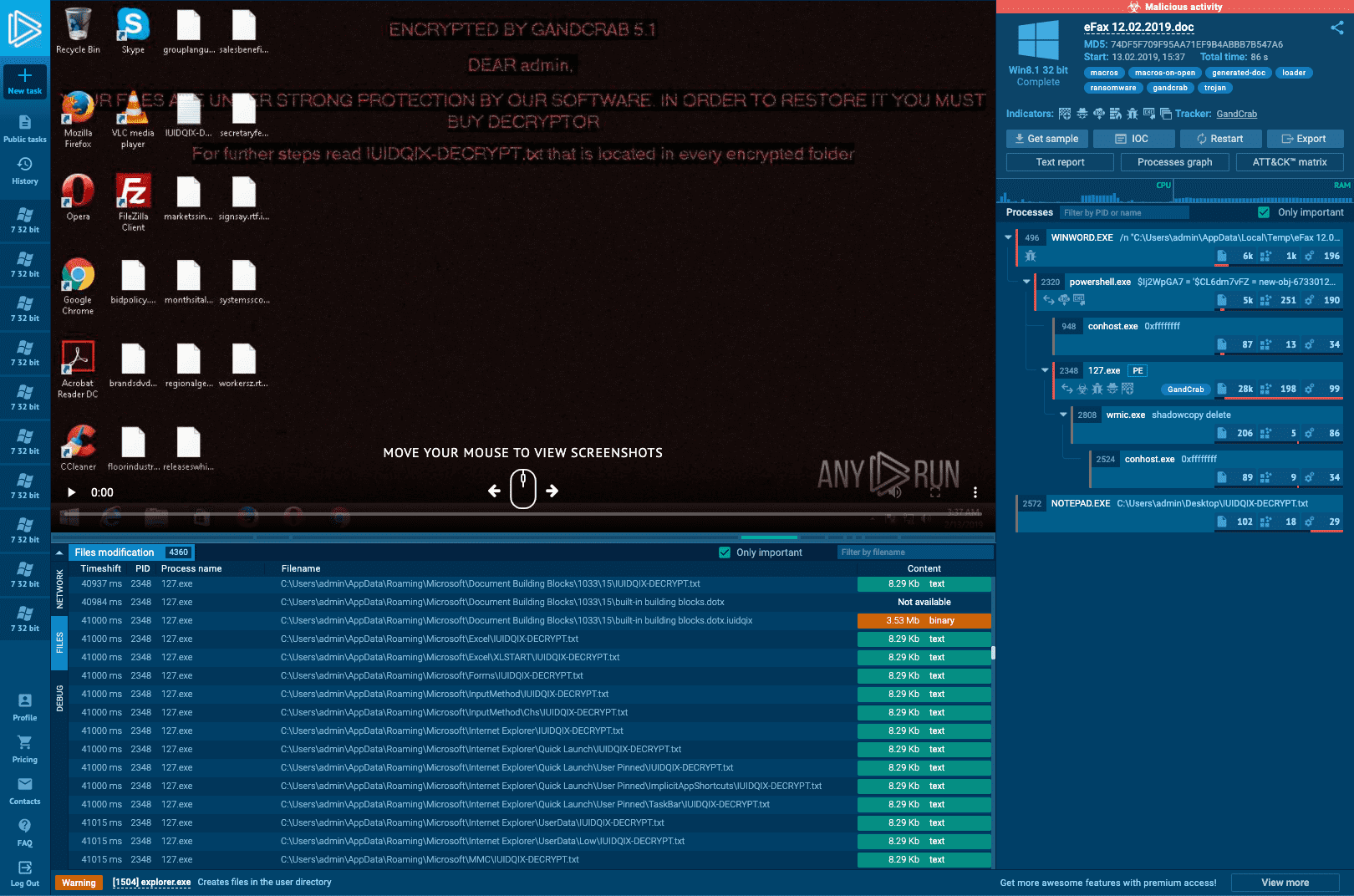
Interactive Online Malware Sandbox

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1

Routers Roasting on an Open Firewall: the KV-botnet Investigation
de
por adulto (o preço varia de acordo com o tamanho do grupo)