Piggybacking Attack in the Context of Cybersecurity
Por um escritor misterioso
Descrição
Piggybacking is a cybersecurity risk that can lead to unauthorized access exploiting legitimate users. Prevent it now!

What is Piggybacking in Cyber Security? Definition, Types & Prevention - CCSLA Learning Academy
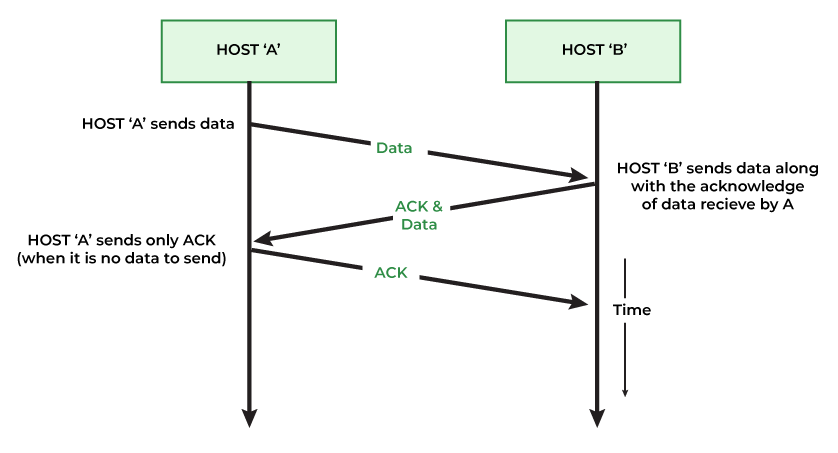
Piggybacking in Computer Networks - GeeksforGeeks
What is Social Engineering?

Threats! What Threats? Command & Control and Stamus Security Platform

PDF] Defining Social Engineering in Cybersecurity

What is Pretexting in Social Engineering?

Pretexting attacks: What are they and how can you avoid them?

Social Engineering in Cyber Security - A Complete Guide

Cyber security of railway cyber-physical system (CPS) – A risk management methodology - ScienceDirect

Module 3-cyber security
What is Social Engineering? Definition + Attack Examples

What Is A Social Engineering Attack? Techniques & Protection - BVA Technology Services
The History Of Cybercrime And Cybersecurity, 1940-2020

What Are Social Engineering Attacks and How to Prevent Them - SEON

Tailgating Attack: What is Tailgating and How to Prevent Unauthorized Access to Your Premises - PSM Partners
de
por adulto (o preço varia de acordo com o tamanho do grupo)