Transforming Self-XSS Into Exploitable XSS
Por um escritor misterioso
Descrição
This blog is describes an attempt by a security researcher to exploit a Cross-site Scripting (XSS) vulnerability. It explains the importance of template strings in XSS filtering, how to overcome the document.domain issue, and the discovery and exploitation of Self-XSS, with reading suggestions.
What is Cross Site Scripting (XSS) ? - GeeksforGeeks
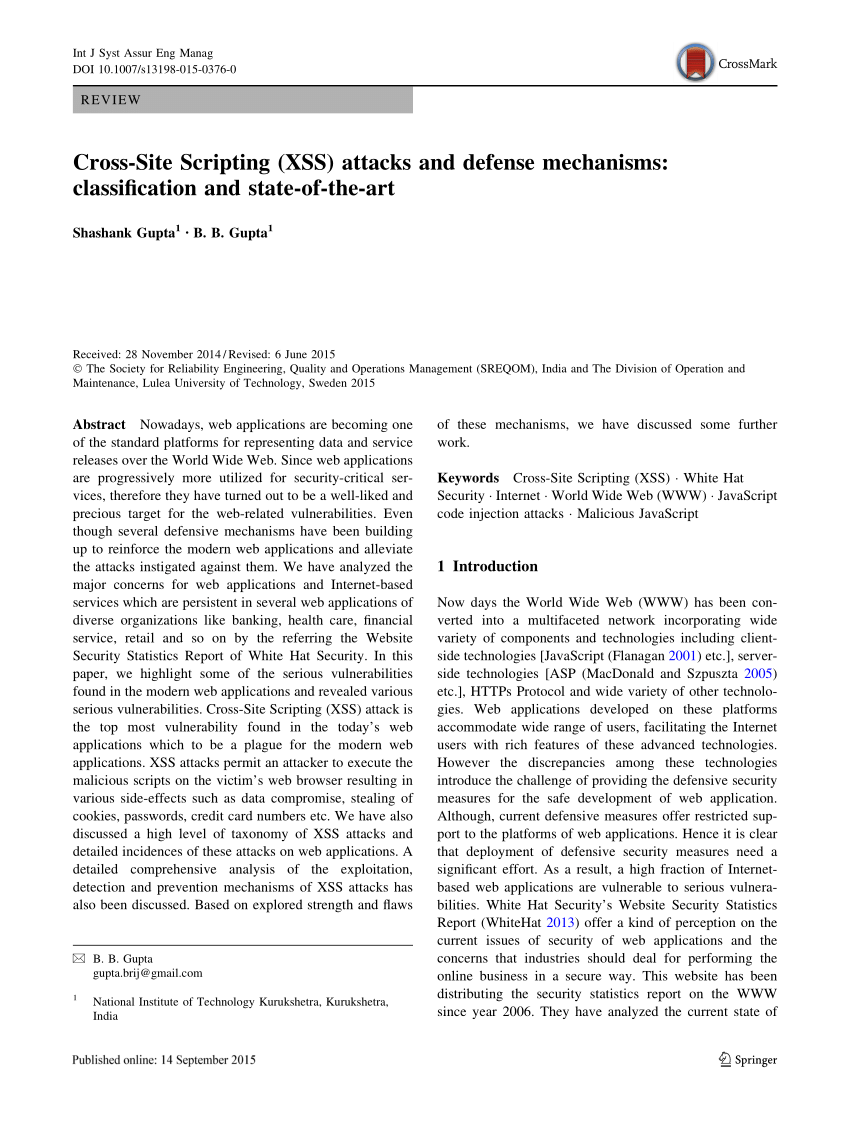
PDF) Cross-Site Scripting (XSS) attacks and defense mechanisms: classification and state-of-the-art
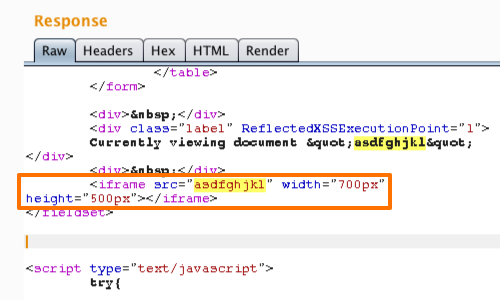
Non-Persistent Cross-site scripting: Non-persistent XSS
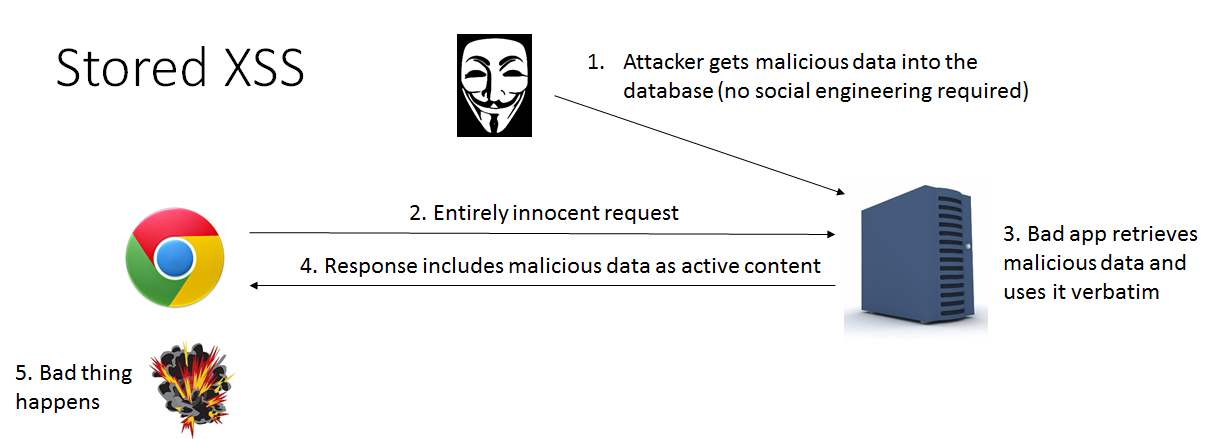
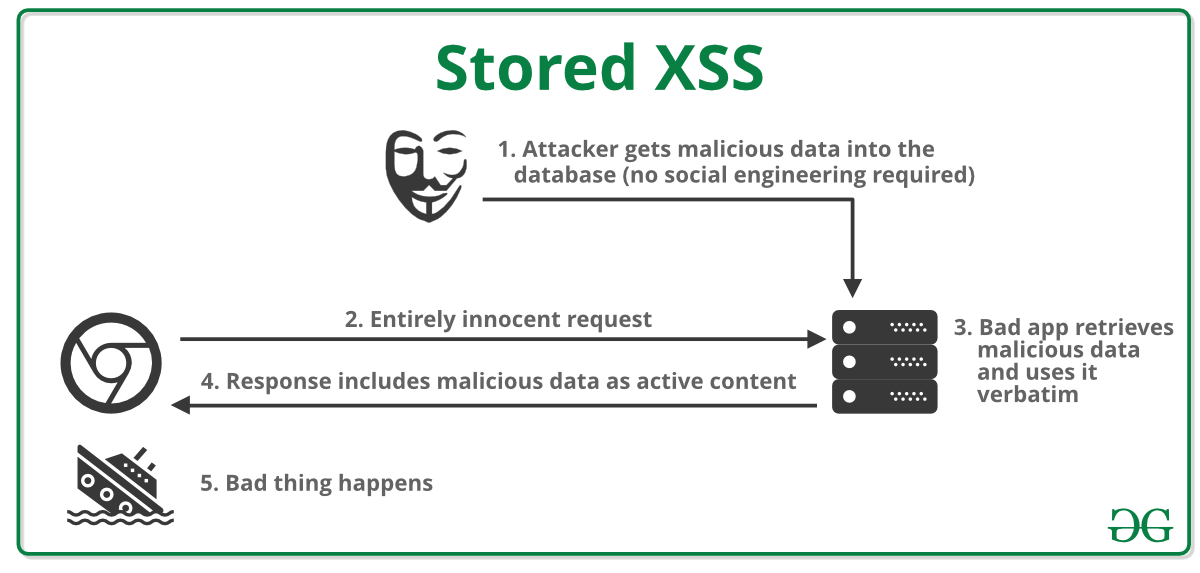
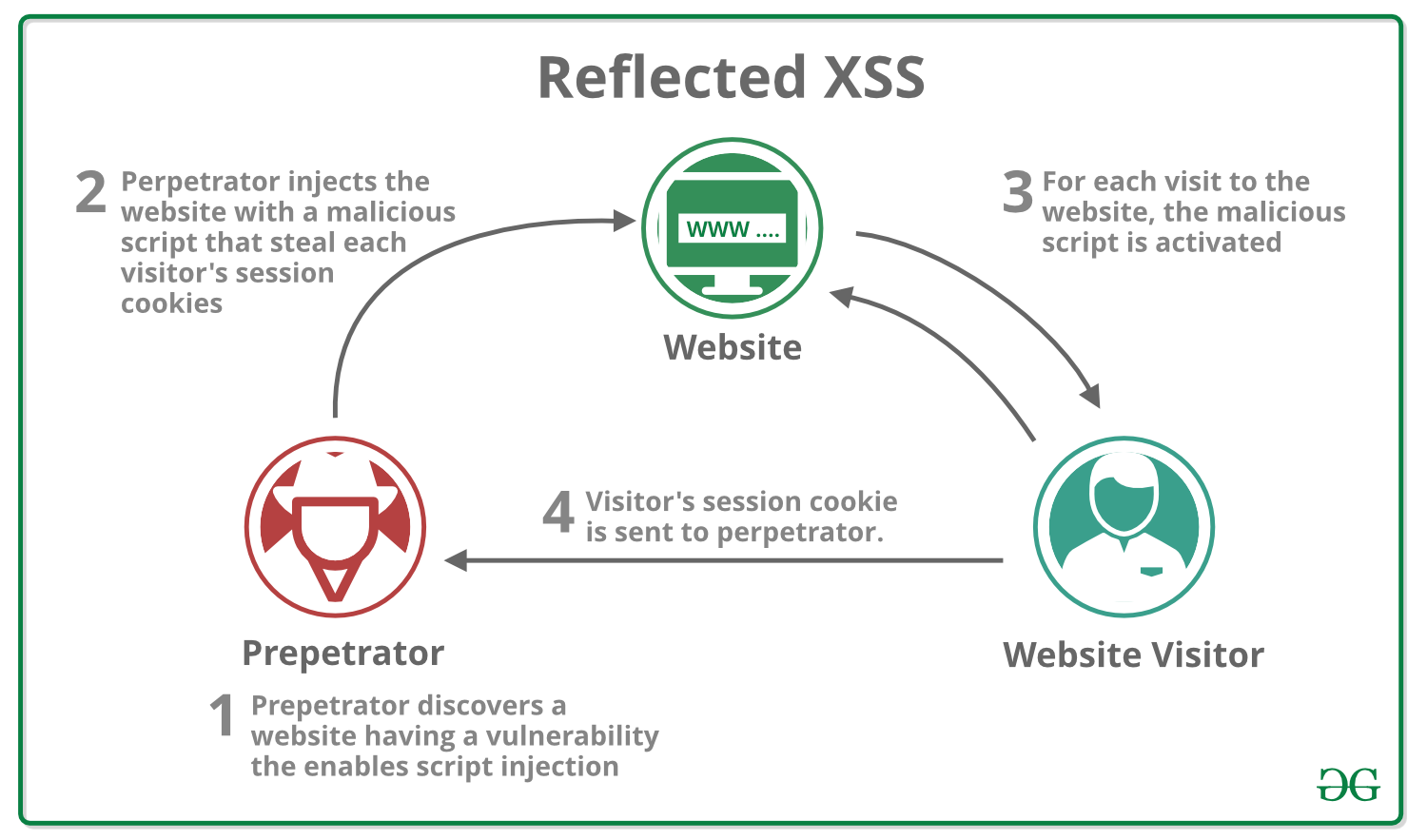
Differences of Stored XSS and Reflected XSS
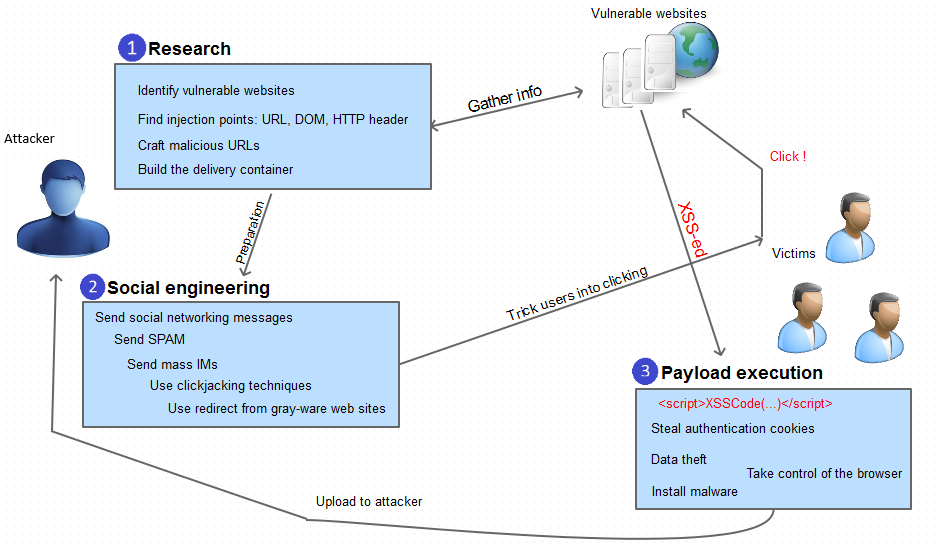
What is a Cross-Site Scripting (XSS) attack: Definition & Examples
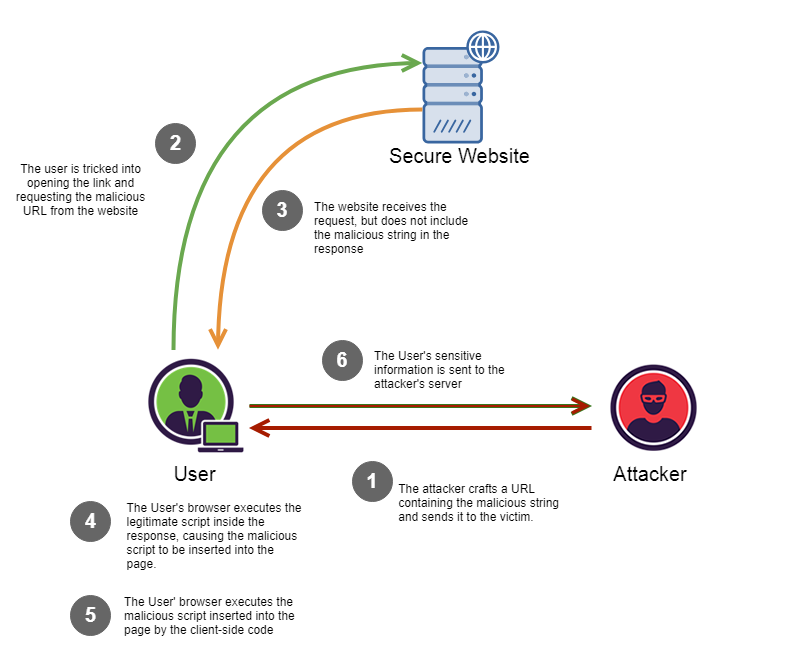
Reflected Cross Site Scripting (r-XSS), by Christopher Makarem, IOCSCAN

Transforming Self-XSS Into Exploitable XSS

Self-XSS - Wikipedia

Transforming Self-XSS Into Exploitable XSS

Bug Bytes #10 - Command Injection, Sublert by @yassineaboukir & Bypassing XSS Detection - Intigriti
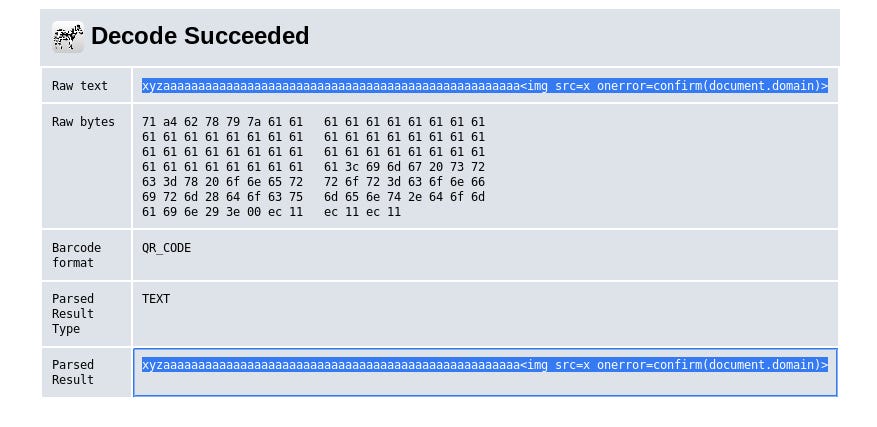
How I was able to turn self xss into reflected xss, by Hein Thant Zin
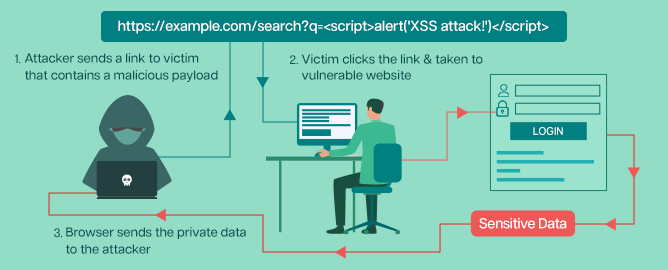
What is Cross-Site Scripting (XSS)? Types of XSS, Examples, and Patching Best Practices - Security Boulevard

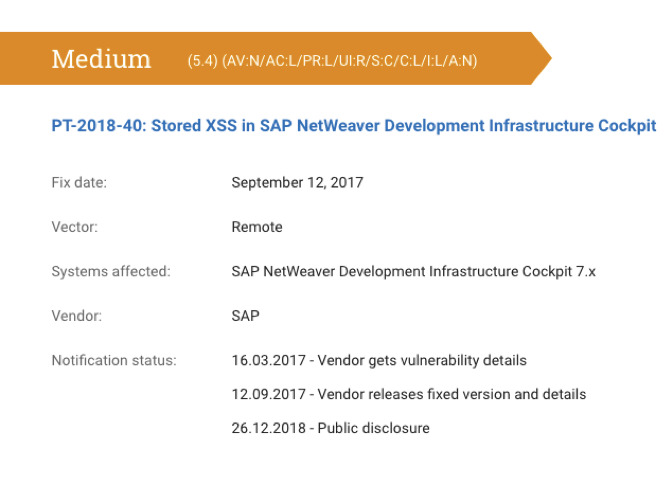
WordPress 5.8.2 Stored XSS Vulnerability
What is Cross Site Scripting (XSS) ? - GeeksforGeeks
What is stored cross-site scripting? - Quora
de
por adulto (o preço varia de acordo com o tamanho do grupo)