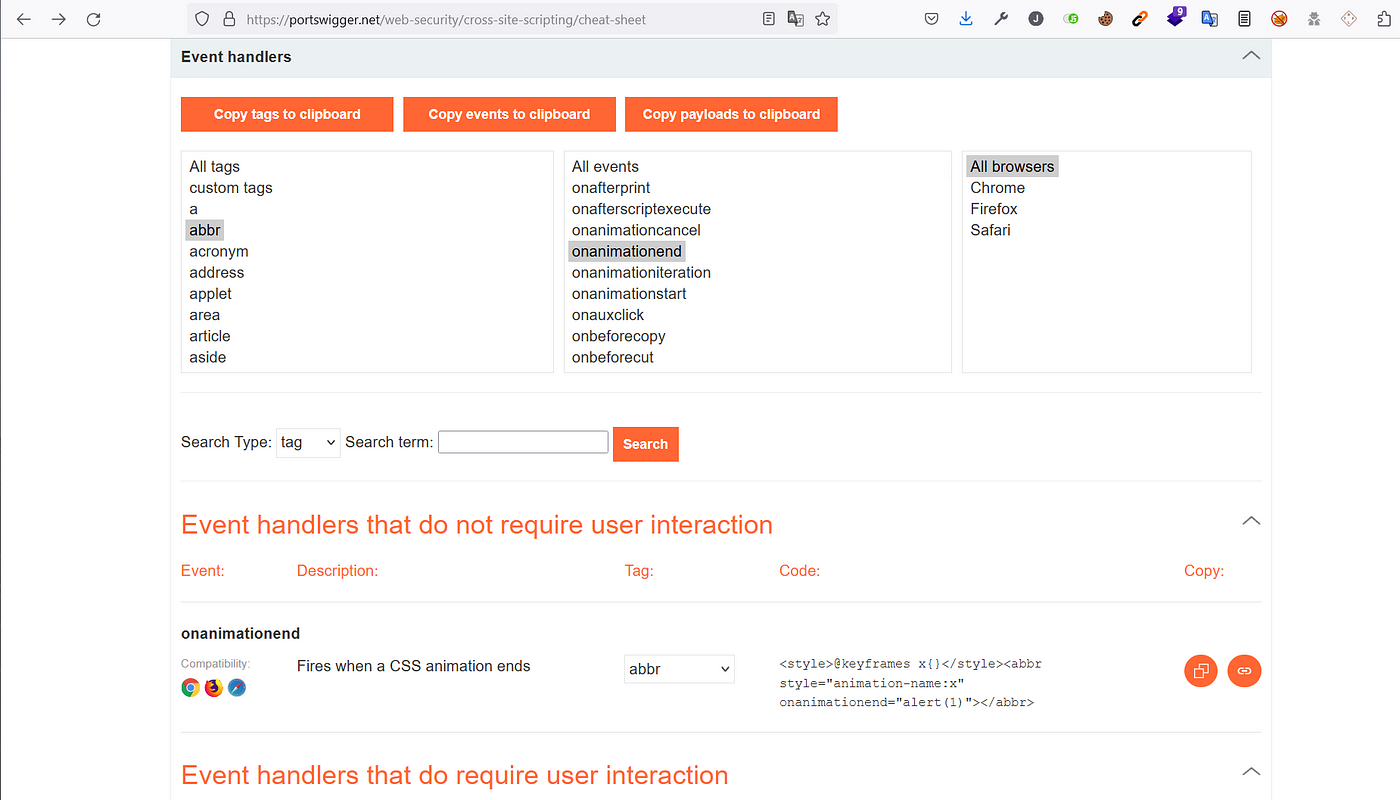
Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes
Por um escritor misterioso
Descrição
This post intends to serve as a guide for a common bypass technique when you're up against a web application firewall (WAF). In the event that the WAF limits what tags and attributes are allowed to be passed, we can use BurpSuite's Intruder functionality to learn which tags are allowed. Table of Contents: Setting the…

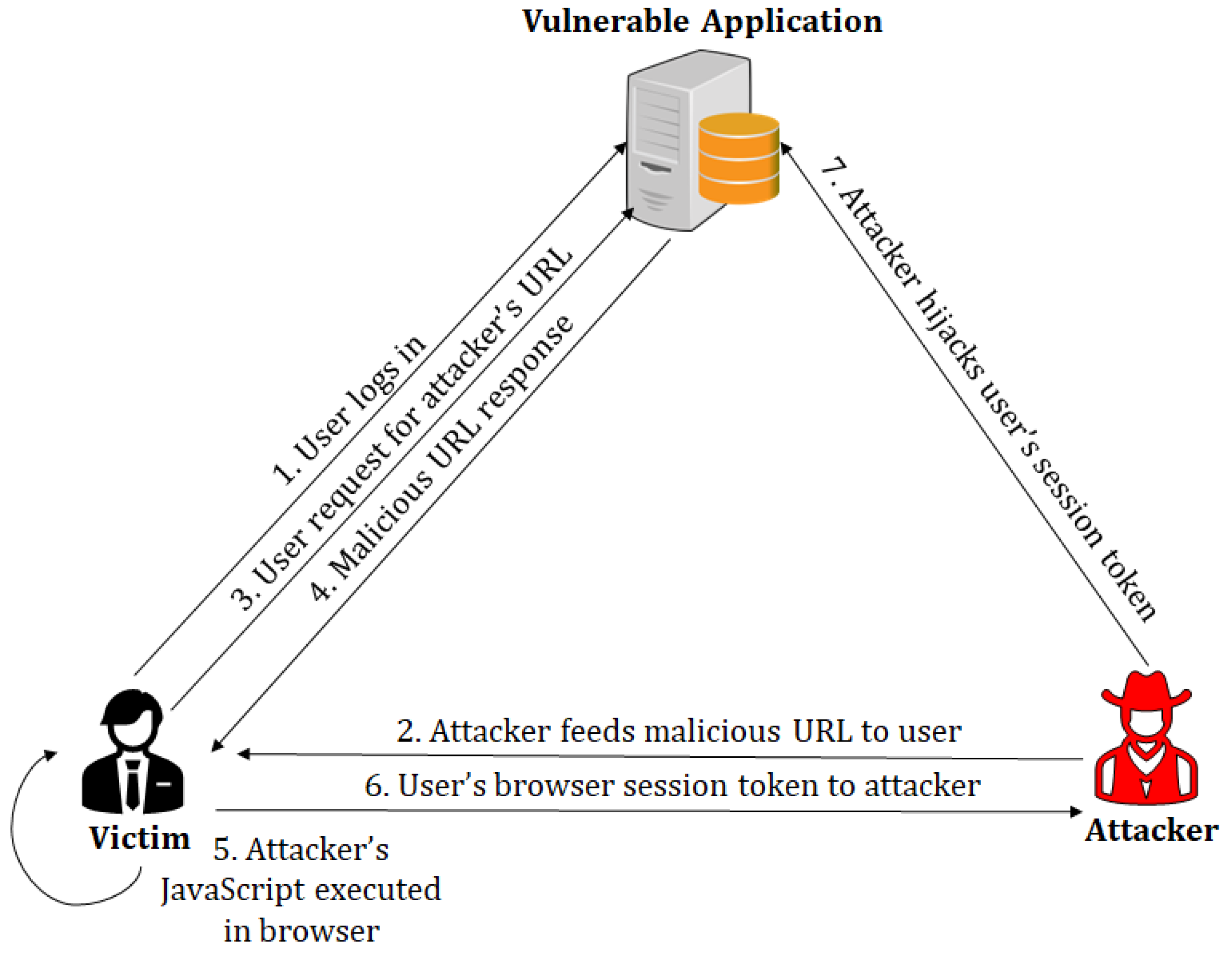
ZTWeb: Cross site scripting detection based on zero trust - ScienceDirect
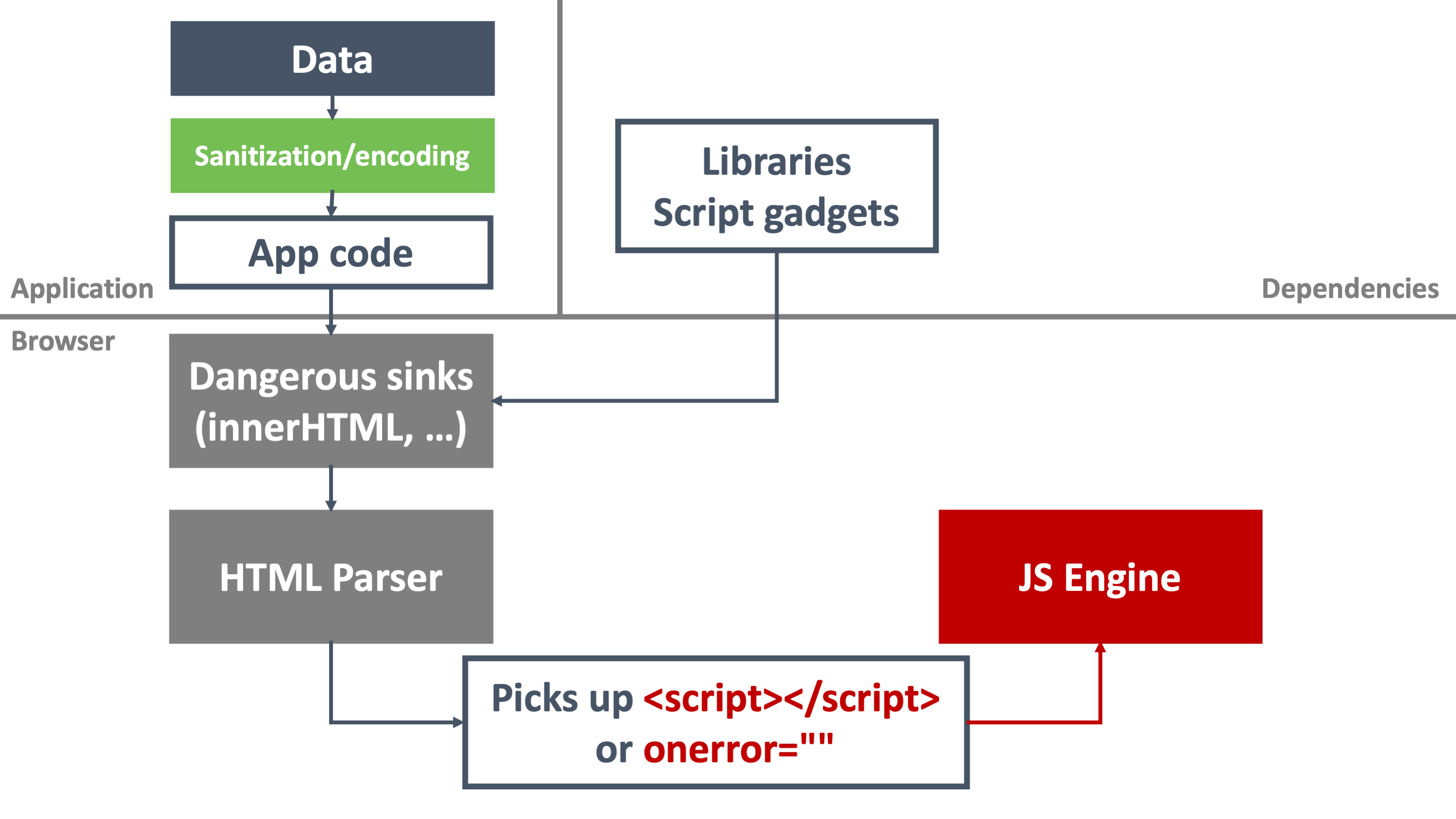
Securing SPAs with Trusted Types
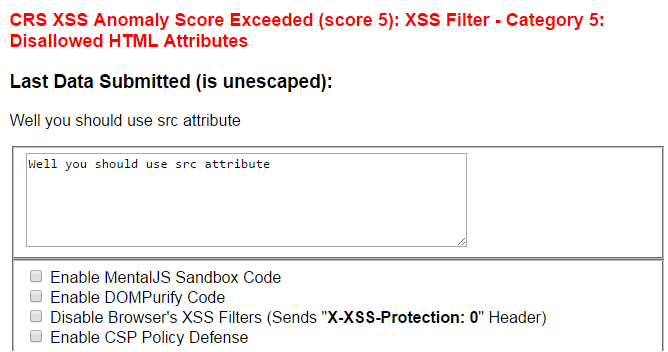
Sucuri WAF XSS Filter Bypass - Miscellaneous Ramblings of a Cyber Security Researcher
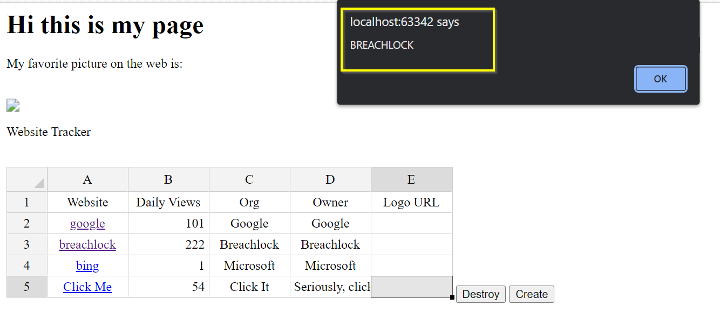
How to Fix XSS Vulnerabilities on Web App Links - BreachLock
Sensors, Free Full-Text
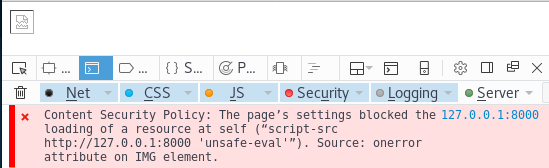
Bypassing modern XSS mitigations with code-reuse attacks - Truesec
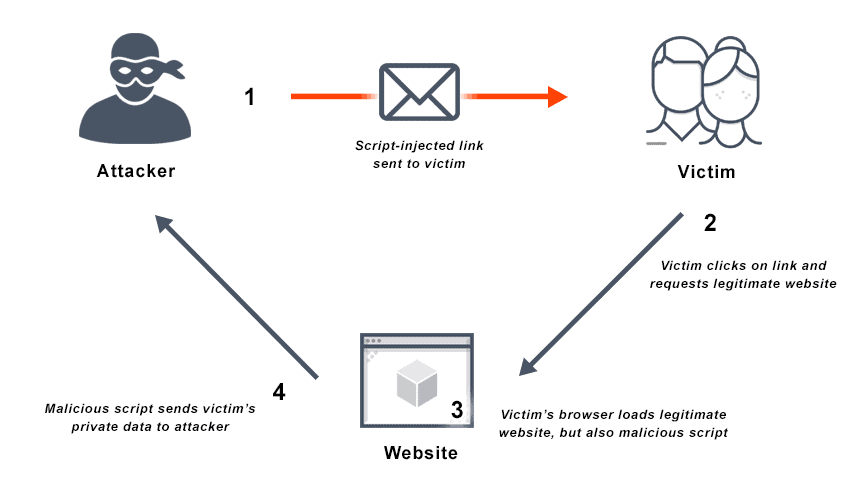
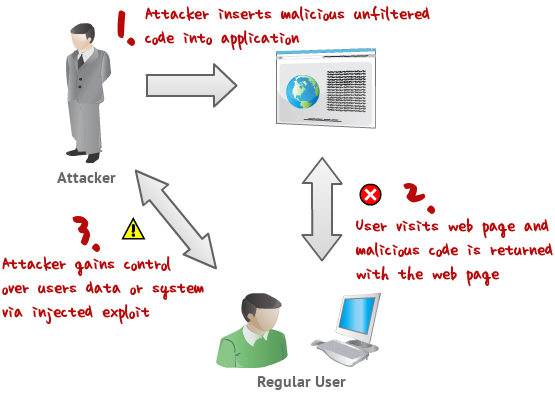
What is Cross Site Scripting? Definition & FAQs

Reflected XSS protected by very strict CSP, with dangling markup attack (Video solution, Audio)
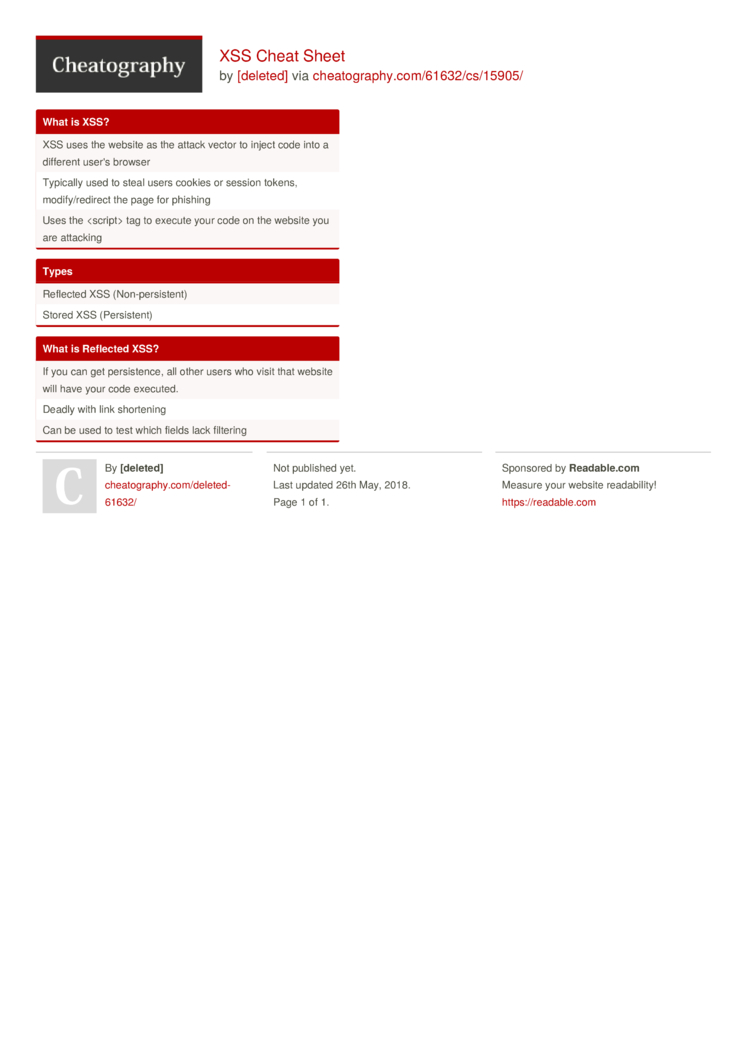
XSS 101 - Brute XSS
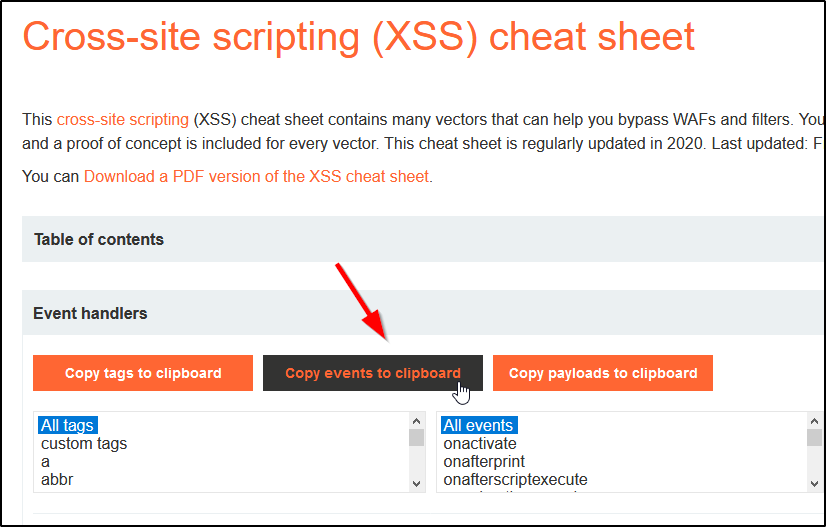
Bypassing XSS Defenses Part 1: Finding Allowed Tags and Attributes
de
por adulto (o preço varia de acordo com o tamanho do grupo)