GootBot - Gootloader's new approach to post-exploitation
Por um escritor misterioso
Descrição
IBM X-Force discovered a new variant of Gootloader — the "GootBot" implant. Learn more about this and how to combat it.

Pratik Raval (PratikR38076335@) / X

38 Million Reasons to use Cryptography for Business - Security Intelligence

Gootloader” expands its payload delivery options – Sophos News

Data Security: How Vulnerable Is Your Critical Data?

How to Shield Targeted Applications from Malicious Exploits

Gootbot: A new post-exploitation implant for lateral movement

New Gootloader Malware Abuses RDP to Spread Rapidly
GootBot: A Stealthy Game Changer in Malware - PureVPN Blog
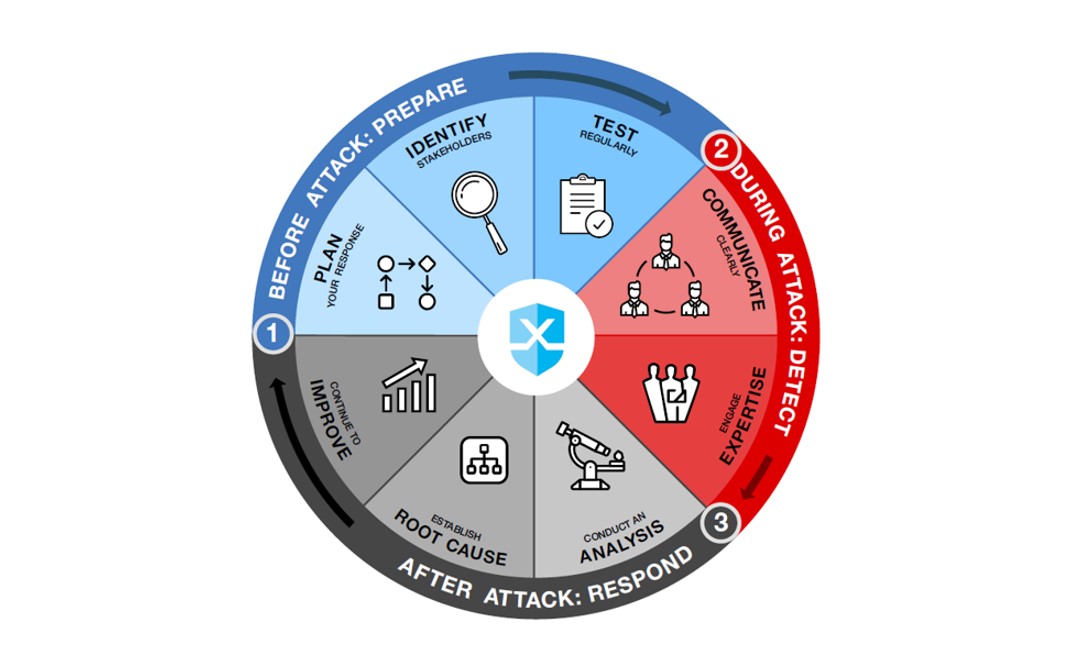
Before, During and After an Attack - Security Intelligence

X-Force (XForce@) / X

9 Post-Exploitation Tools for Your Next Penetration Test

Prashant Uniyal 🇮🇳 (@prashant_92) / X

Trusteer Rapport Effectively Resists Carberp Bypass Attempts
de
por adulto (o preço varia de acordo com o tamanho do grupo)






