How can an attacker execute malware through a script? 2022
Por um escritor misterioso
Descrição
Script-based malware. How to stay protected? – Gridinsoft Blog

PC malware statistics, Q3 2022
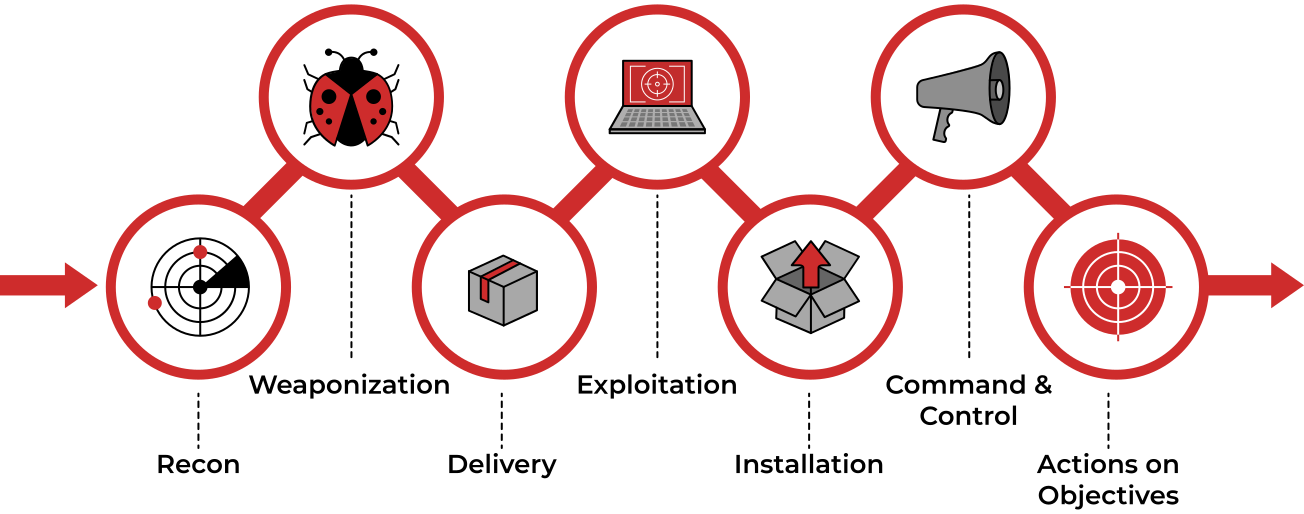
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is…, by Haircutfish

How Malware Works 2022
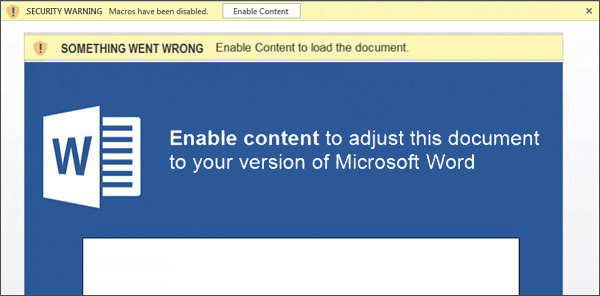
Script-based malware. How to stay protected? – Gridinsoft Blog
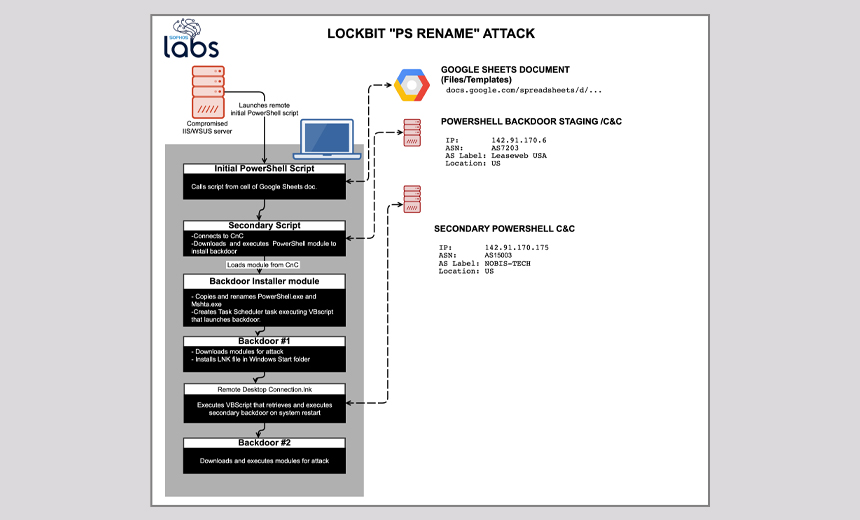
LockBit Ransomware Uses Automation Tools to Pick Targets
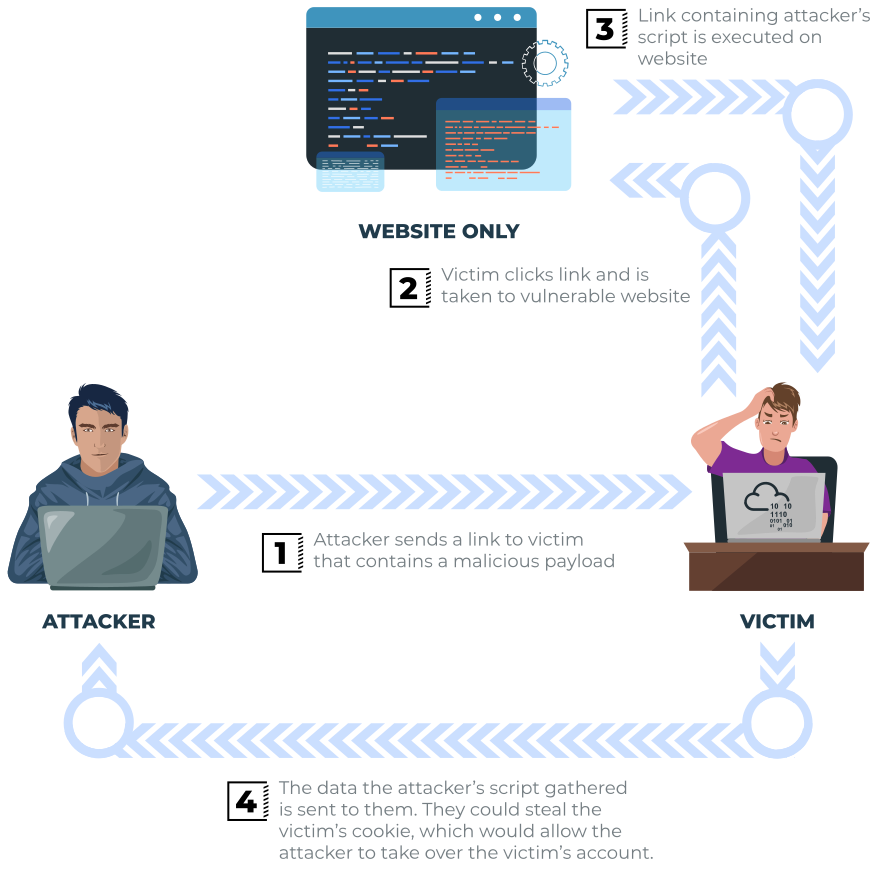
TryHackMe: Cross-Site Scripting. This is a walk through of TryHackMe's…, by Critical0x

SQL injection and cross-site scripting: The differences and attack anatomy
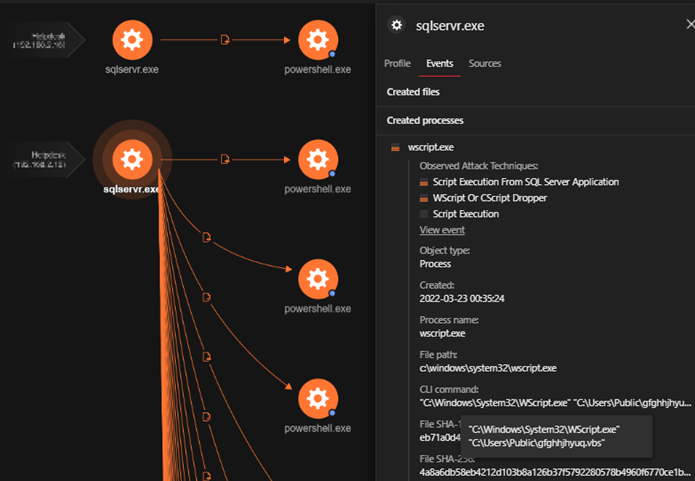
Uncovering a Kingminer Botnet Attack Using Trend Micro Managed XDR
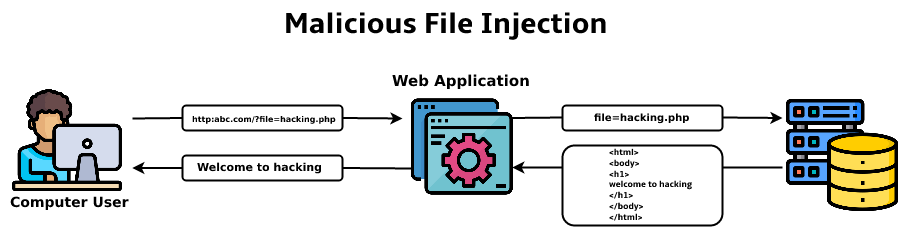
What is Malicious File Execution? - GeeksforGeeks
Fileless Malware: The Complete Guide

Script-Based Attacks - How Can an Attacker Execute Malware Through A Script? - Computer Repair

Attack Graph Response to US-CERT Alert (AA22-174A): Malicious Cyber Actors Continue to Exploit Log4Shell in VMware Horizon Systems - AttackIQ
de
por adulto (o preço varia de acordo com o tamanho do grupo)