Learning from cyber security incidents: A systematic review and
Por um escritor misterioso
Descrição
Cyber security incidents are now prevalent in many organisations. Arguably, those who can learn from security incidents and address the underlying cau…

How to Create an Incident Response Plan (Detailed Guide)
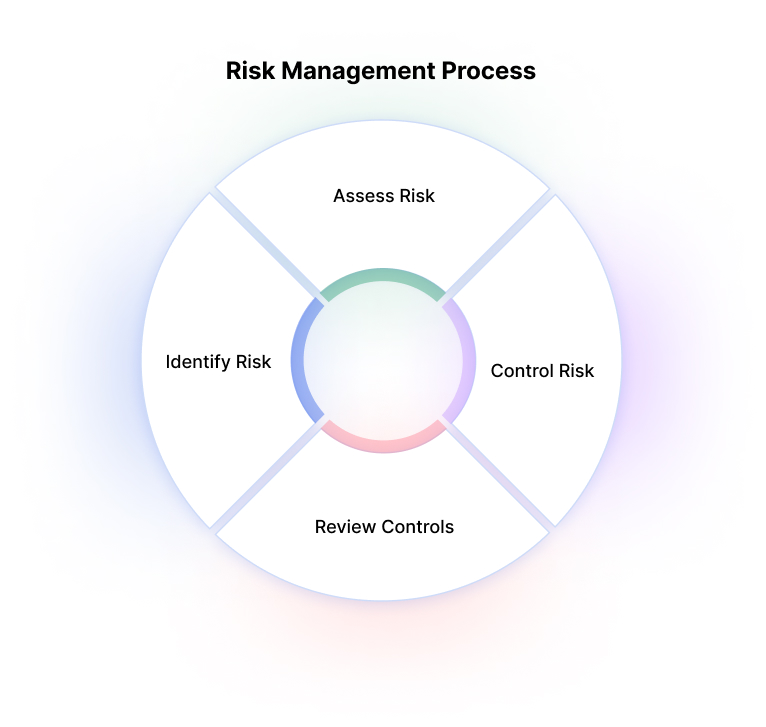
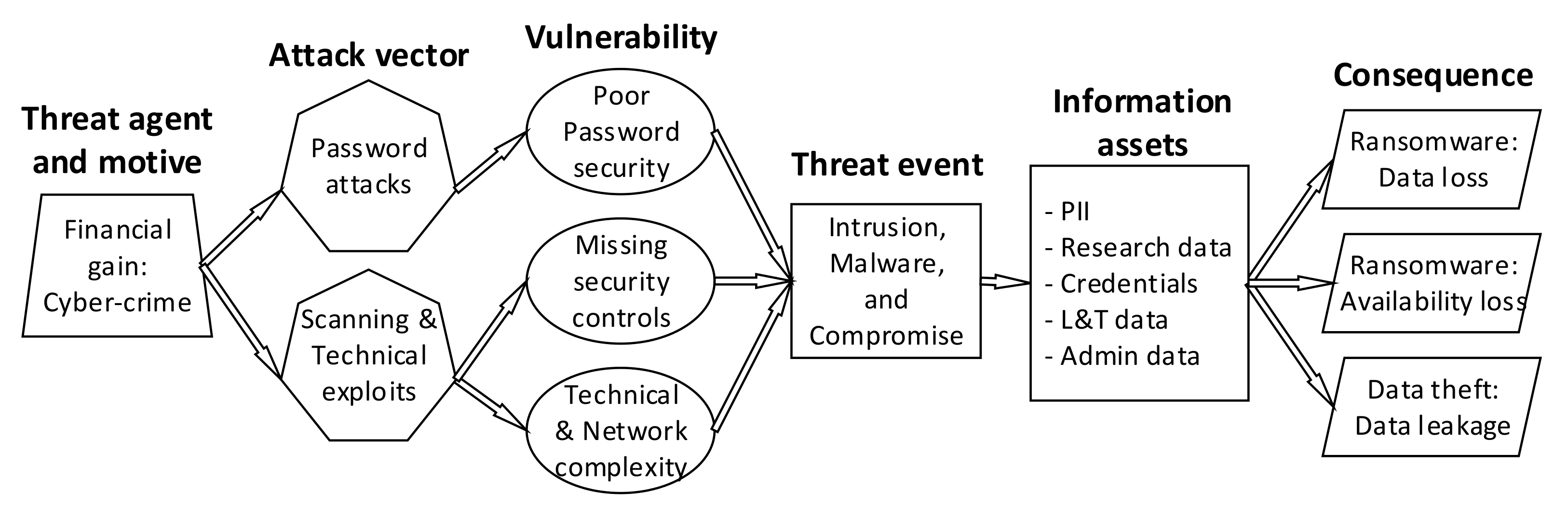
Cybersecurity Risk Management Frameworks, Analysis & Assessment

Top 10 Best-Known Cybersecurity Incidents

6 Incident Response Steps to Take After a Security Event

Learning from cyber security incidents: A systematic review and
Future Internet, Free Full-Text

What is the future of cybersecurity?
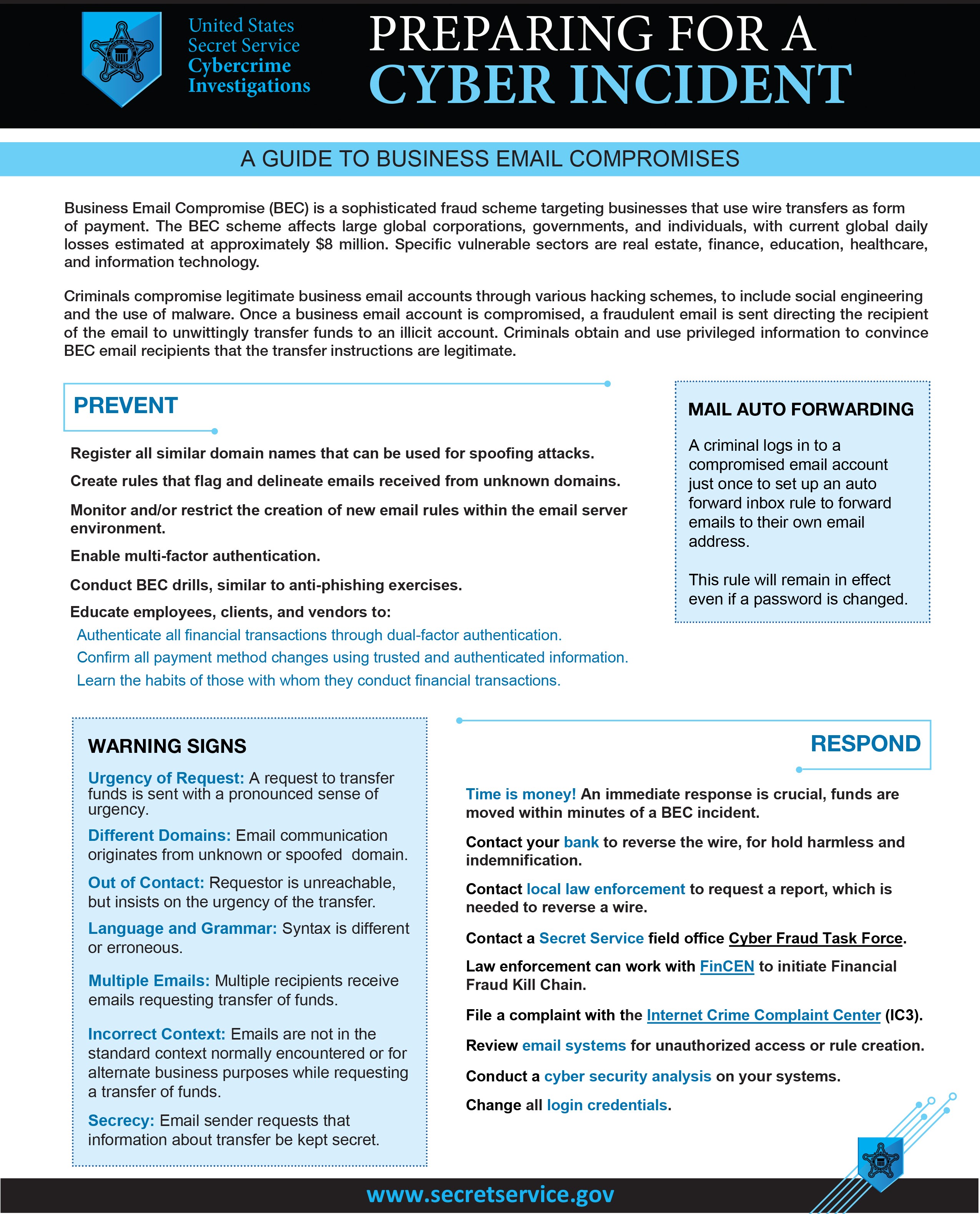
Preparing for a Cyber Incident

Red Teams vs. Blue Teams: What's The Difference?
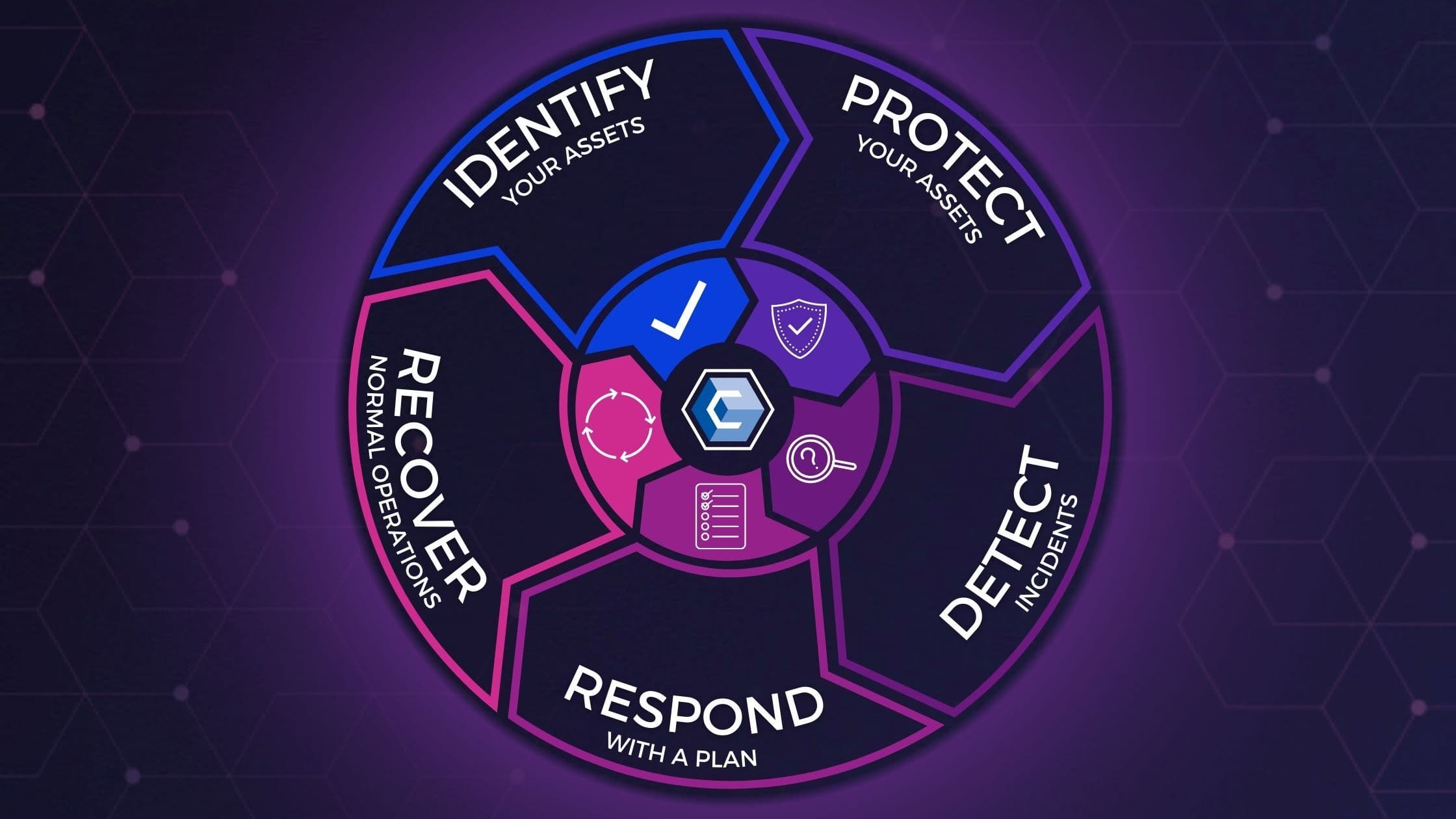
Reviewing the 5 Stages of the Cybersecurity Lifecycle [+ EXAMPLES]

Cybersecurity trends: Looking over the horizon

Sensors, Free Full-Text
PDF) A Systematic Review of Cybersecurity Risks in Higher Education

Checking-up on Health: Ransomware Accounts for 54% of
Vulnerability in Cyber Security - A Step-by-Step Guide for Beginners
de
por adulto (o preço varia de acordo com o tamanho do grupo)