Hundreds of Microsoft sub-domains open to hijacking
Por um escritor misterioso
Descrição
Experts demonstrated that hundreds of Microsoft sub-domains could potentially be hijacked and abused to deliver malware and for phishing attacks
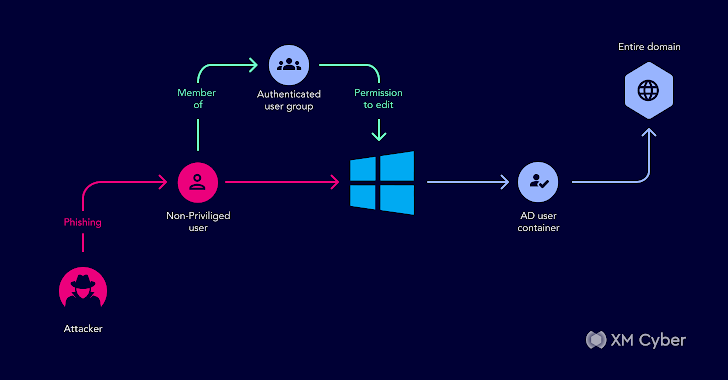
Understanding Active Directory Attack Paths to Improve Security

Don't let subdomains sink your security
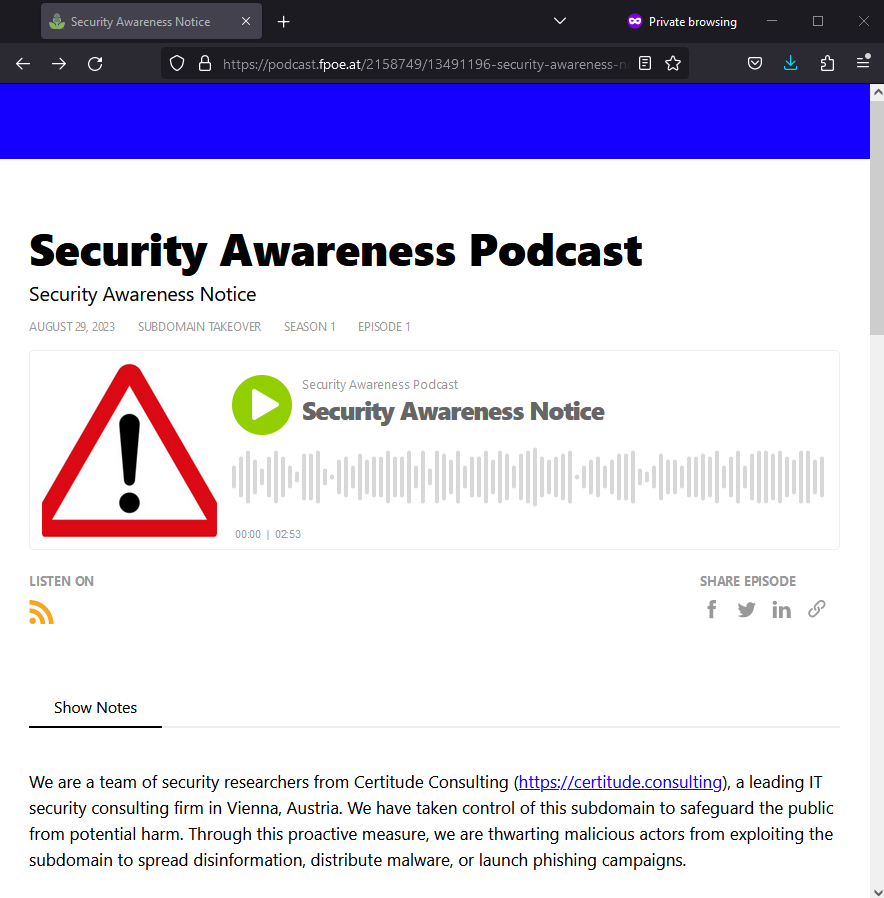
Thousands of Organizations Vulnerable to Subdomain Hijacking – Certitude Blog
What is a DNS Attack? Types of DNS attacks & preventing them

Cybercriminals Using EvilProxy Phishing Kit to Target Senior Executives in U.S. Firms
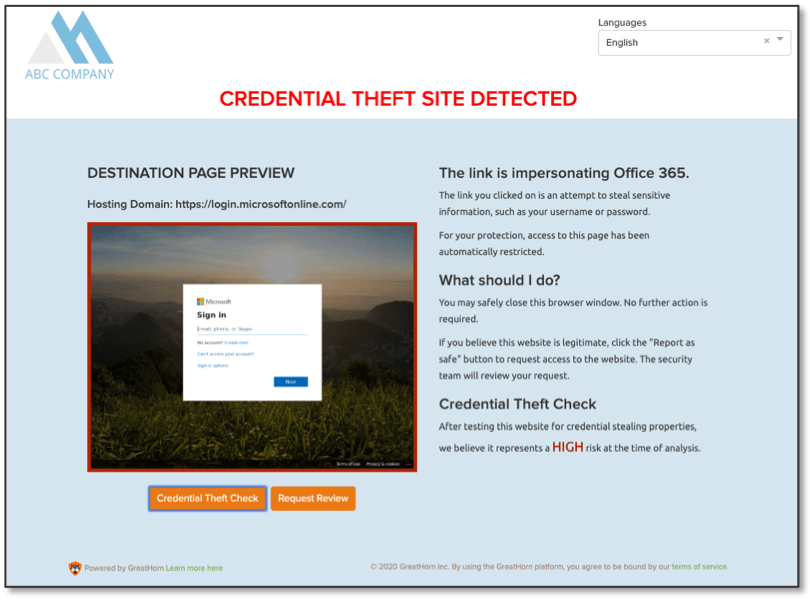
How to Protect Against Microsoft Subdomain Takeover - GreatHorn
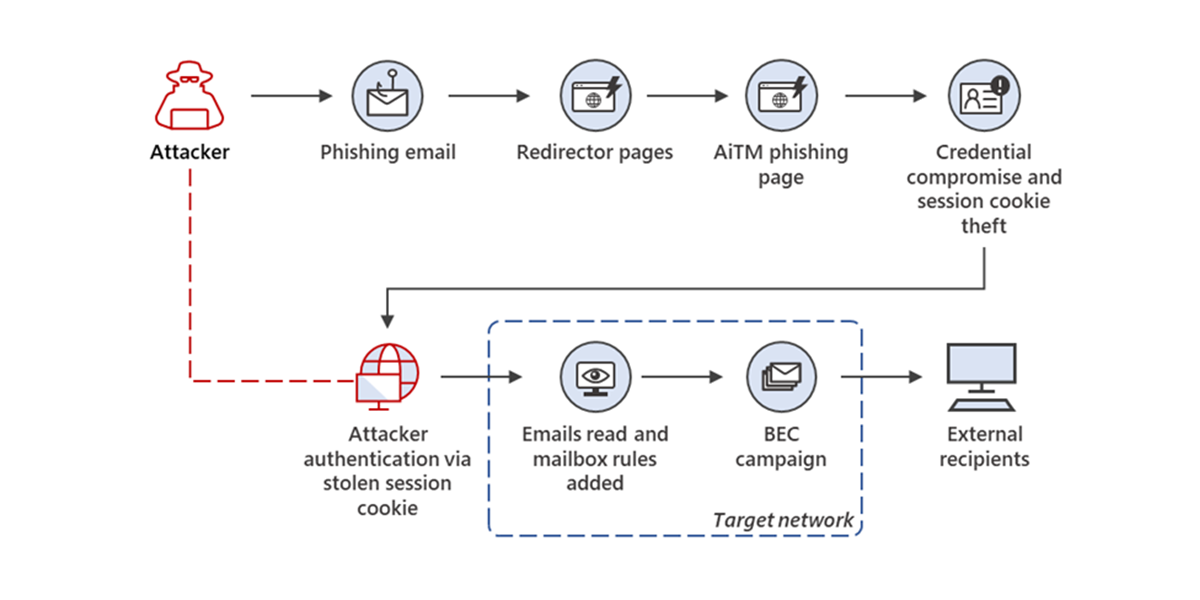
From cookie theft to BEC: Attackers use AiTM phishing sites as entry point to further financial fraud
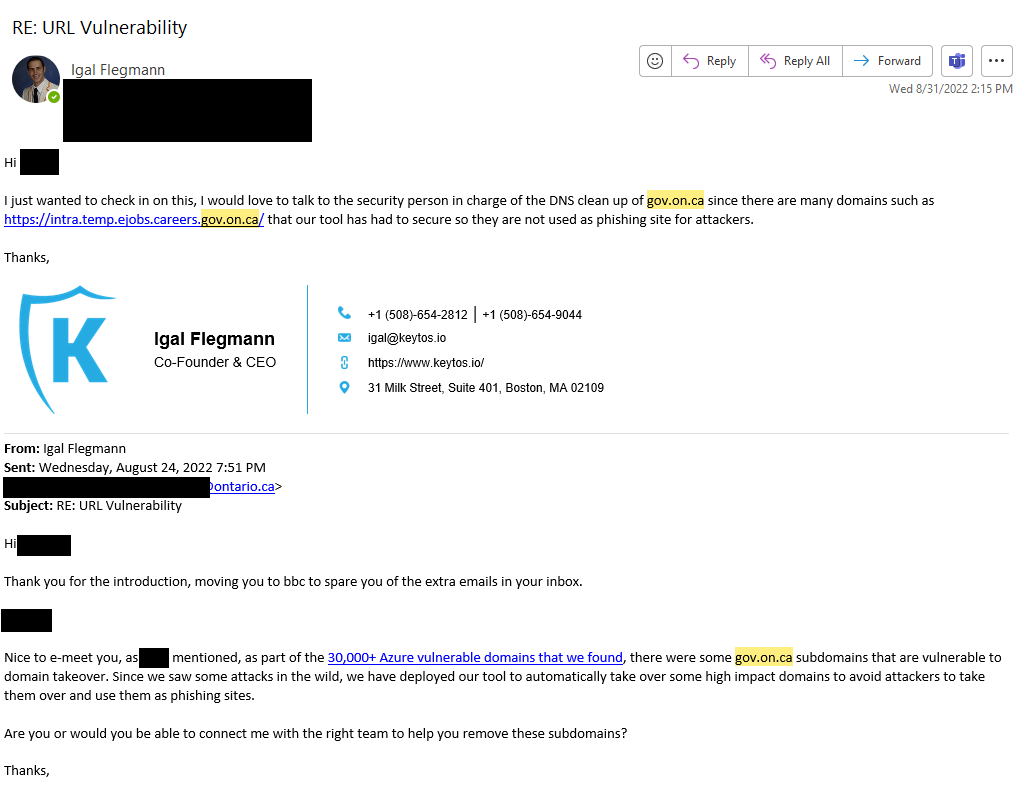
Microsoft Azure Vulnerability Still Affecting Thousands of New Subdomains Each Month

Microsoft has a subdomain hijacking problem

A Microsoft 365 feature can ransom files on SharePoint and OneDriveCould
de
por adulto (o preço varia de acordo com o tamanho do grupo)