window.open(url, name) is vulnerable to XSS with name collision · Issue #262 · w3c/html · GitHub
Por um escritor misterioso
Descrição
Xiaoran Wang (xiaoran@attacker-domain.com) This is a joint research with Travis Safford. window.open(url, name, [args]) makes it easy for websites accepting user supplied URLs to be vulnerable when attackers can cause a collision on the
AppSec-Labs, Application Security

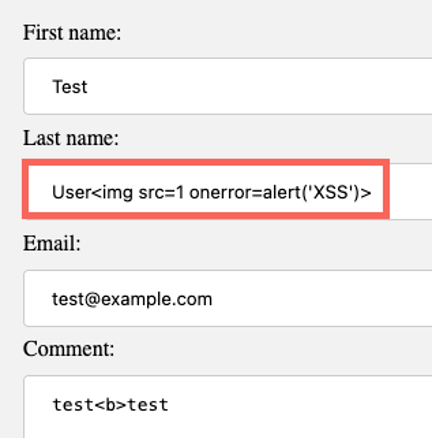
Persistent XSS (unvalidated Open Graph embed) at LinkedIn.com, by Jonathan Bouman

How We Found Another XSS in Google with Acunetix

Ckan, PDF, File Format

eclipse - The type org.openqa.selenium.chrome.ChromeDriver is not accessible - Stack Overflow
GitHub Desktop unable to fetch (url has no scheme) · Issue #9597 · desktop/desktop · GitHub
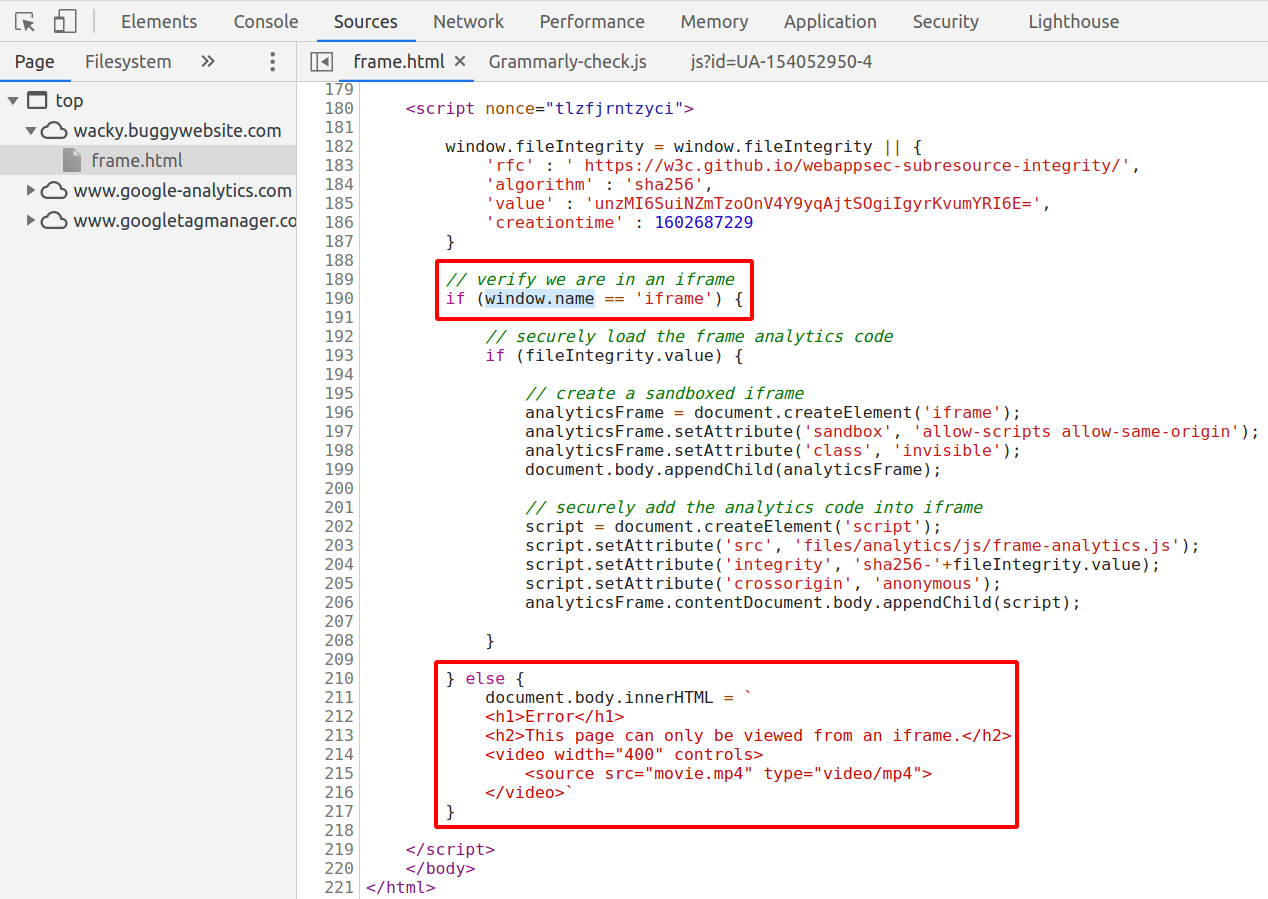
Wacky XSS challenge write-up. On November 4th BugPoc published a new…, by Daniel Santos

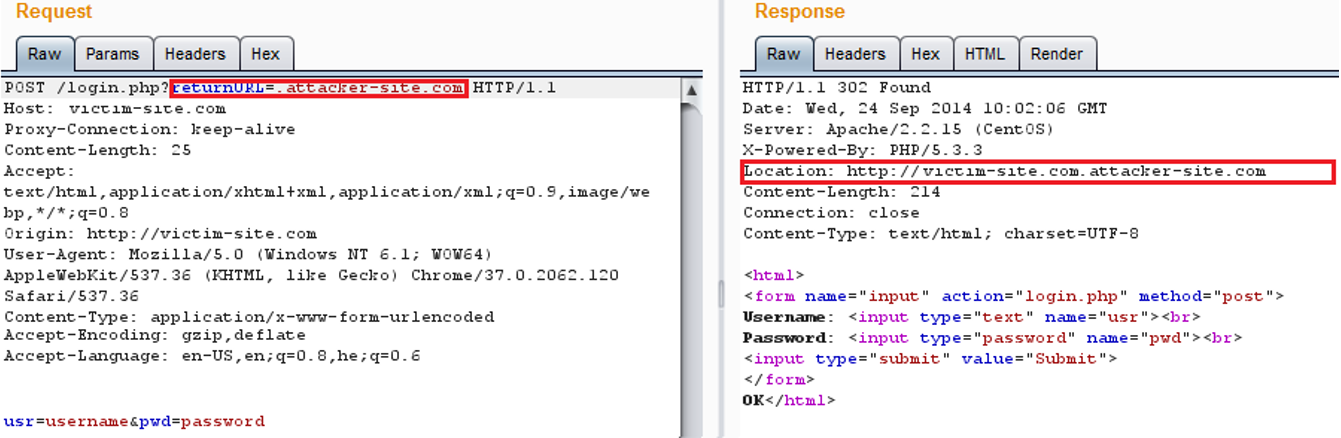
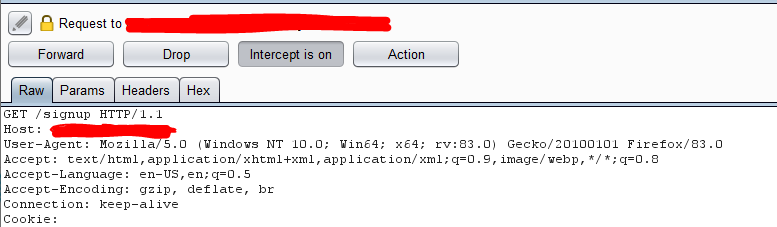
Initial Access with XSS and HTML Smuggling - Theory
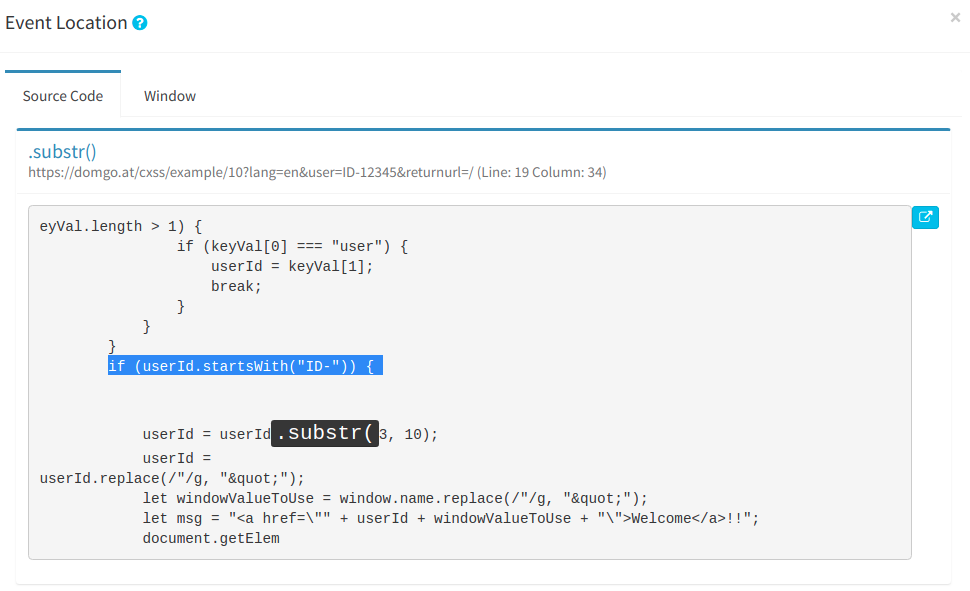
Automating Discovery and Exploiting DOM (Client) XSS Vulnerabilities using Sboxr — Part 3, by Riyaz Walikar
GitHub - Snorlyd/https-nj.gov---CVE-2020-11022: Vulnearability Report of the New Jersey official site
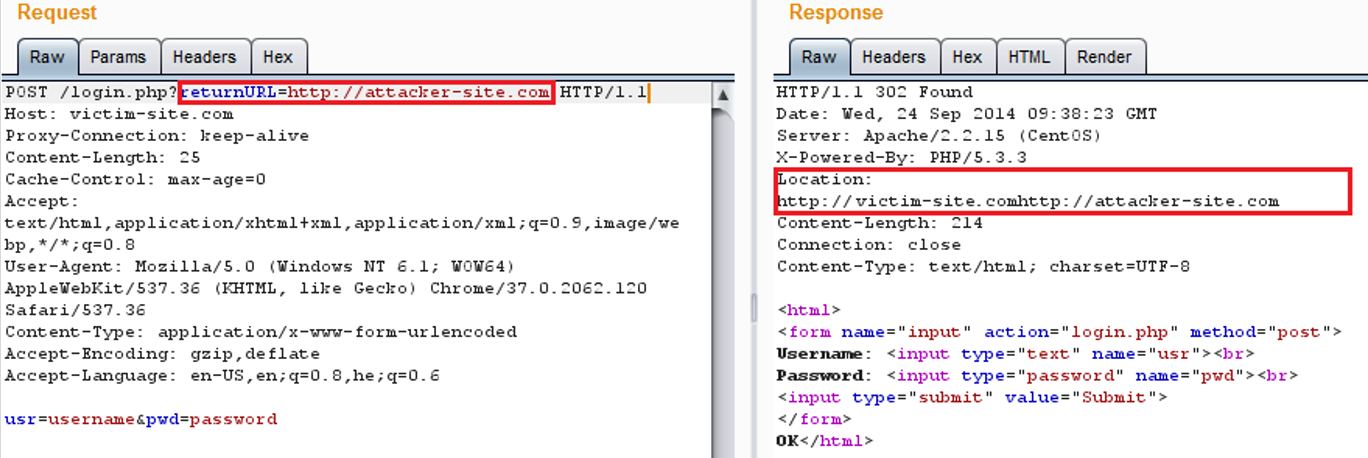
AppSec-Labs, Application Security
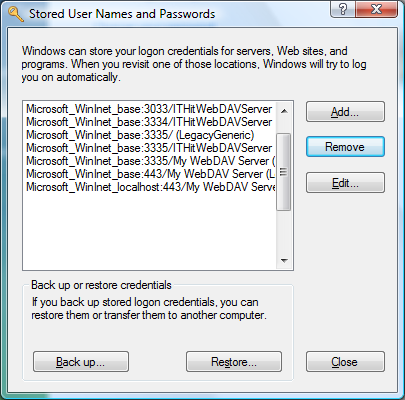
Connecting to WebDAV server on Microsoft Windows
No module named 'external.nms' · Issue #52 · xingyizhou/CenterNet · GitHub

Automating Discovery and Exploiting DOM (Client) XSS Vulnerabilities using Sboxr — Part 3, by Riyaz Walikar
XSS-Reflected (User_Agent). This is my first blog so, in this blog…, by Syed Munib Ahmed
de
por adulto (o preço varia de acordo com o tamanho do grupo)